With security breaches reaching worldwide news on an almost monthly basis, FIM or file integrity monitoring tools have become crucial for businesses to run securely. These tools are used to prevent data leaks to competitors and malicious agents.
Here is our list of the top nine File Integrity Monitoring Tools:
- SolarWinds Security Event Manager – FREE TRIAL This tool operates as a SIEM and also tracks changes to files, folders, and registry keys to observe file movements and shares. Runs on Windows Server.
- ManageEngine Log360 – FREE TRIAL This collection of security services includes tracking of user activity on the network and endpoints, including network shares. Available for Windows Server.
- SolarWinds Server & Application Monitor – FREE TRIAL A monitoring system that offers security templates to track activities on files stored on the network and on cloud platforms. Runs on Windows Server.
- ManageEngine ADAudit Plus – FREE TRIAL This is an activity tracking system that includes file integrity monitoring on Windows Server. Available for Windows Server, AWS, and Azure.
- CrowdStrike Falcon FileVantage This file monitor is delivered from the cloud and can centralize the monitoring of multiple locations.
- OSSEC A HIDS that scours log files for security threats and tracks changes to important files. Available in free and paid versions that run on Unix and Linux.
- Trustwave Endpoint Protection A package of security tools that includes file integrity monitoring. Delivered from the cloud.
- Tripwire A FIM that can be tailored to specific data security standards and is part of a cloud platform of security tools that slot together.
- QualysGuard FIM This tool eases FIM by automatically detecting specific files that need to be protected in order to meet specific data security standards. This is a cloud-based system.
What Is File Integrity Monitoring?
FIM is a type of security measure which deals exclusively with files that have been tampered with. This type of software will generally capture an image of your entire system, and then at regular intervals compare that image to what is on it currently.
If there is an unauthorized change detected(for example, a user that doesn’t have access permissions opening a file.) It can immediately alert you, or even act against it itself.
In this article, we’ve assembled the best pieces of file integrity monitoring software to come out this year, so take a look at our in-depth guide below.
Here’s the Best File Integrity Monitoring Tools & Software of 2024:
1. SolarWinds Security Event Manager – FREE TRIAL
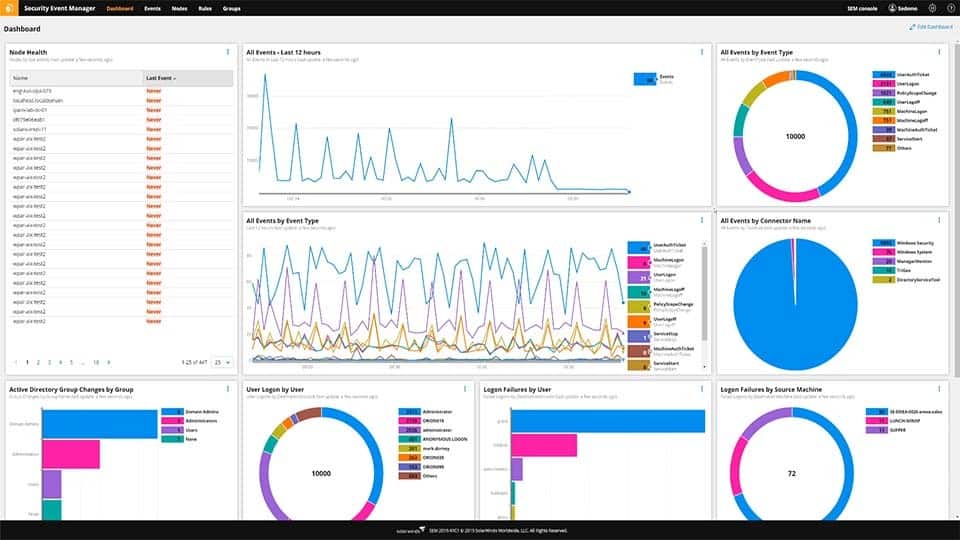
Coming in at number 1 we have SolarWinds Security Event Manager. It can be easily summarized as a business-oriented tool that helps centralize all of your information to have quality FIM. This tool features SIEM(Security information and event management) monitoring capabilities in real-time, and will quickly inform you of any suspicious activity within your files.
The tool will show you who changed what within your files, as well as any other user activity, which will, in turn, allow you to customize your alert system so that it only notifies you if there’s something actually going on. Furthermore, this tool will go beyond what is usually expected of an FIM tool. This is our top pick for what tool you should entrust your business’ data and files to. This is in part due to its extremely streamlined and intuitive interface. For example, you’ll see that the sidebar on the homepage will show you the number of changes made under the “Change Management” section. You can also easily filter through different events by using keywords, making filtering out noise a breeze.
Main Features:
- It helps you centralize and normalize all of your log-collection into one tool.
- It will automatically detect and respond to almost all threats
- It has compliance-reporting tools built into it from the get-go
- The UI is sleek and easy to use
- Licensing it is a simple, and relatively inexpensive process
The SolarWinds also features a variety of compliance within it as soon as you get it, which is excellent for regulated businesses, or those with an abundance of sensitive information.
Price: You can start with a 30-day free trial.
Download: https://www.solarwinds.com/security-event-manager/registration
2. ManageEngine Log360 – FREE TRIAL
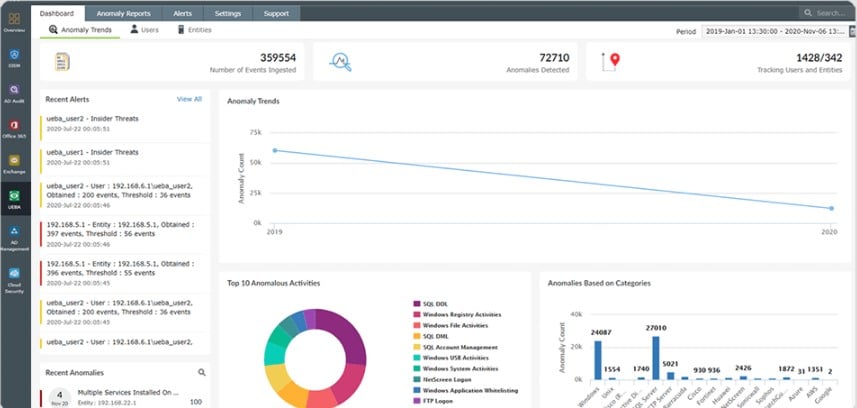
ManageEngine Log360 is a bundle of security systems. Each of the six components included in the package is also available for purchase individually. Two of the system included in the Log360 collection perform file integrity monitoring.
The first of the two FIM systems in Log360 is provided by EventLog Analyzer. This is a log server and manager that provides a data viewer with analytical tools in it. The EventLog Analyzer FIM includes a configuration planner in which the user specifies the types of objects that need to protect. Once operating, the FIM records every action on protected files and notes which user account was involved. The system includes user behavior analytics (UBA), which defines a pattern of regular activity n files per user account. Divergence from this standard provokes an alert for a possible insider threat.
The second unit that delivers FIM is ADAudit Plus. This service also includes UBA as a detection mechanism. This tool focuses on the protection of Active Directory instances and logs access and changes to domain controllers.
Price: There is a Free edition for log360, which offers the same services as the paid version, which is called Premium, but with volume restrictions. The software for Log360 runs on Windows Server and you can try the Premium edition with a 30-day free trial.
Download: https://www.manageengine.com/log-management/download.html
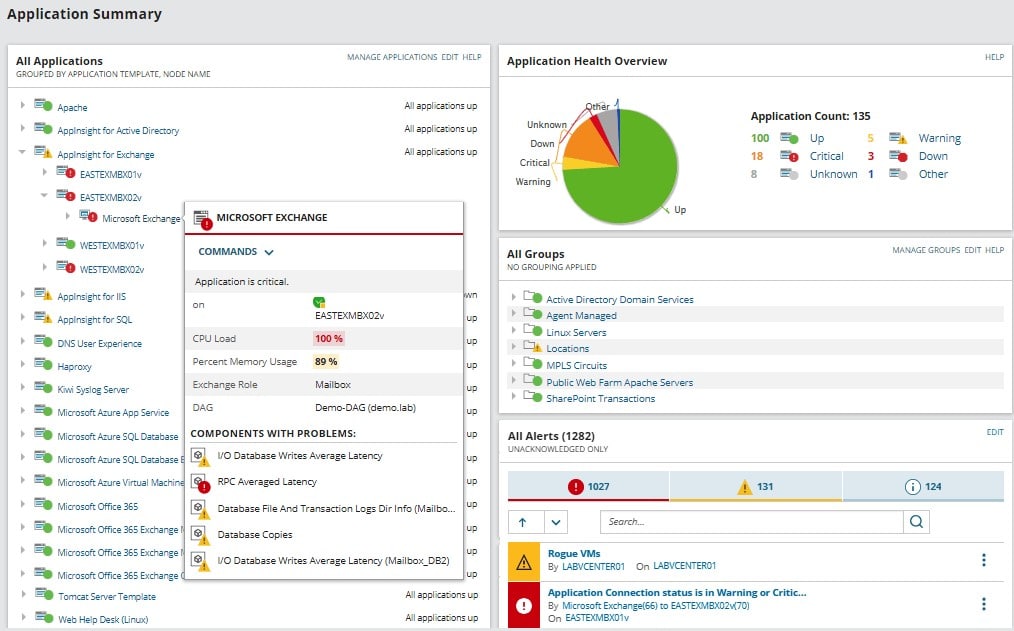
3. SolarWinds Server & Application Monitor – FREE TRIAL
The SolarWinds Server & Application Monitor is an extremely versatile tool, allowing you to monitor your systems regardless of their OS. Furthermore, it can monitor both from an on-premise installation and from a variety of cloud options. There are over 1200 ready-made templates in the tool, containing vendor applications, databases, as well as other pieces of infrastructure. The excellent thing about this is that you don’t need too much technical know-how in order to get this done.
Main Features:
- You can get started within minutes of installing the tool
- It’ll allow you to monitor Azure, AWS, IaaS, PaaS, and SaaS
- There are over 1200 ready-made templates that come in-built, with the SolarWinds community being responsible for over 1000 more
- It allows you to customize your monitoring with a variety of scripts(PowerShell, Rest API, WMI, SNMP)
- It features infrastructure dependency mapping
This tool is excellent for beginners or those that need a very customized approach to their monitoring. If you’re a beginner, you’ll find it quite easy to find a template that does all you need it to. On the other hand, a larger business might need an extremely precise and customized approach to their FIM, which is what this tool is for.
Price: 30-day Free Trial
Download: https://www.solarwinds.com/server-application-monitor
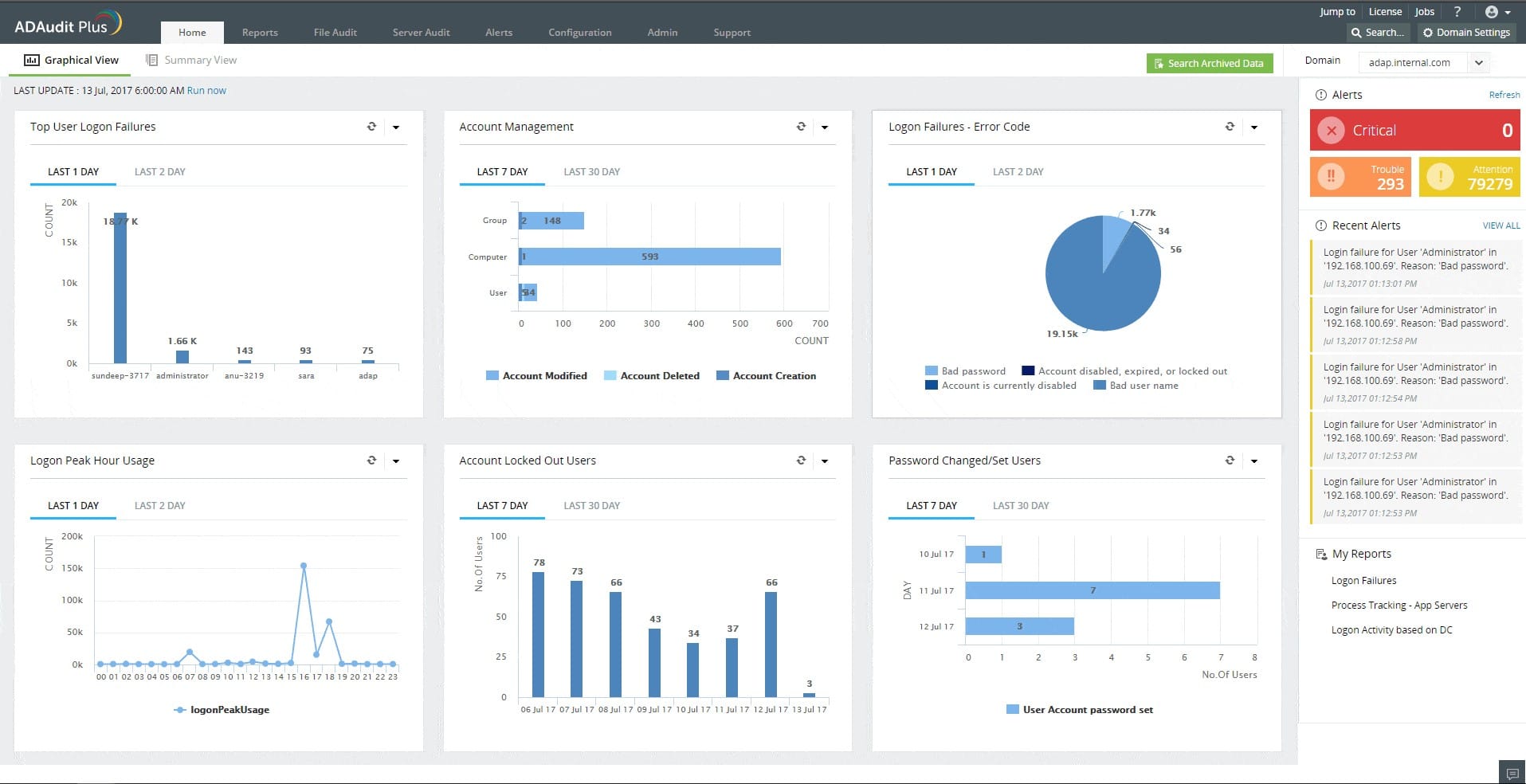
4. ManageEngine ADAudit Plus – FREE TRIAL
ManageEngine ADAudit Plus tracks user activities on servers and also protects Active Directory values from unauthorized changes. The package protects servers running Windows and that means an AD instance running on Windows Server, reaching across the network to control permissions for files and directories on Windows devices. This system implements logging of all file access by users.
Main Features:
- Continuous file integrity monitoring that covers operating system, database, and software data files plus logs and reports
- User file access activity logging
- System file protection
- Report searches and analysis
- Compliance reporting for GLBA, HIPAA, SOX, GDPR, and PCI DSS
The file change tracking can be set to raise an alert for specific types of actions, such as a sudden surge in file encryption activity, which would indicate a ransomware attack. Each action on the system has to be implemented through a user account and so the system logs the account that is associated with each file access and change. Records of activities can be sorted and filtered by user account, which will immediately show if a single account has suddenly gone rogue. This report will identify account takeover actions.
Price:
- Free edition: $0
- Standard edition: From $595
- Professional edition: From $945
Download: Get a 30-day free trial at https://www.manageengine.com/products/active-directory-audit/
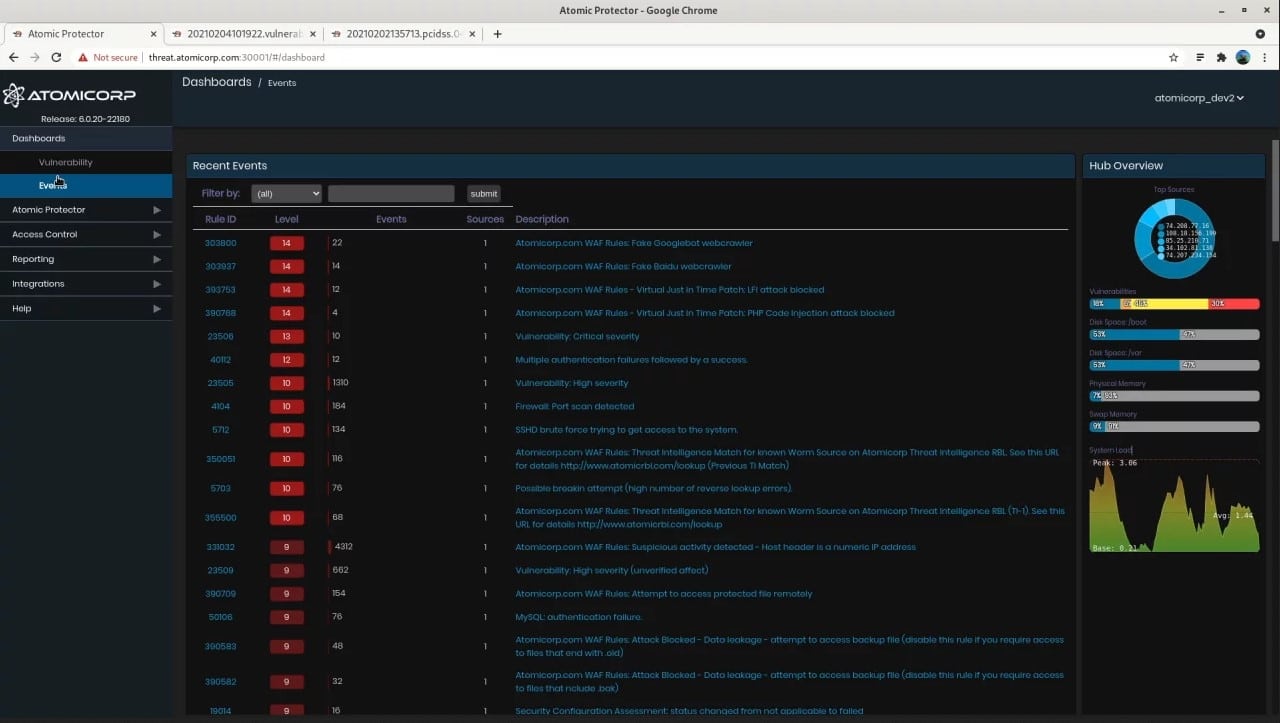
5. CrowdStrike Falcon FileVantage
CrowdStrike Falcon FileVantage is a cloud-based system that forms part of a platform of cybersecurity services. The tool is able to supervise activity on files on multiple sites simultaneously, enabling you to centralize data security. The system logs all actions on files, recording the user account involved.
Main features:
- Easy to set up
- Activity summary page
- The ability to narrow the focus of monitoring on specific files
- A guided security policy creation system
- Optional threat intelligence feed
- Compliance with PCI DSS, CIS, and SOX
This tool is a useful system for tracking activities on files. However, it doesn’t include a sensitive data locator or categorizer. The system is delivered on the same platform as an entity detection and response system and also an XDR, so it would be very easy to assemble a comprehensive suite of cybersecurity tools in the same environment.
Pricing: Access a 15-day free trial.
Download: CrowdStrike Falcon FileVantage does not require a download because it is a cloud service. Access more information at https://www.crowdstrike.com/products/security-it-operations/falcon-filevantage/
6. OSSEC
OSSEC is one of the most common starting points in the world of file integrity monitoring. This is an open-source tool marketed as an intrusion detection system on Linux and Mac. This tool has an in-built file-monitoring function which OSSEC titled Syscheck.
The default setting for this is for it to run every 6 hours and check if there have been any changes made to the files that you’ve selected. This is done this way in order to ensure that the tool doesn’t occupy too much CPU power. If you’re looking for an FIM tool that only takes a small toll on your CPU, this might be the one for you.
With that being said, OSSEC does have its weaknesses. For example, if you’re using Windows you’ll soon find that OSSEC only has a server-agent mode for windows, rendering many of its functionalities moot.
Like most other open-source programs, OSSEC has superior, paid alternatives. However, if you’re not quite ready to make the jump yet, here’s what OSSEC gives you.Main Features:
- It’s free and open-source, making it a great pick for smaller businesses or individual projects.
- Has two modes: serverless and server-agent, both of which are useful.
- While its Windows support isn’t ideal, it is miles better than most free Windows alternatives.
- It can respond to any intrusions in real-time, applying firewalls, integrating with 3rd party content, and taking self-healing actions.
All in all, OSSEC is an excellent tool to start out with, however, large-medium businesses that stick with it long-term are few and far in between.
Download: https://www.ossec.net/ossec-downloads/
7. Trustwave Endpoint Protection
The Trustwave Endpoint Protection tool is a cloud-based tool that, while useful for FIM, is not primarily geared towards it. Because of this, it is significantly pricier than an FIM-exclusive tool. If you’re looking for one tool to handle FIM, log monitoring, incident management, etc. then you’ll find that kind of versatility here.
Main Features:
- It’s an extremely easy tool to set up and install
- You can easily access Trustwave SIEM information
- Trustwave customer support is responsive and helpful
- It has built-in PCI reporting and compliance
With all of this being said, if you aren’t looking for advanced features outside of the scope of FIM, then this tool might just be too complex for you. While it is quite good in an enterprise setting due to the visibility across a variety of data sources it gives, its pricy nature makes it a hard sell for any other business.
Download: https://www.trustwave.com/en-us/services/managed-security/threat-detection/
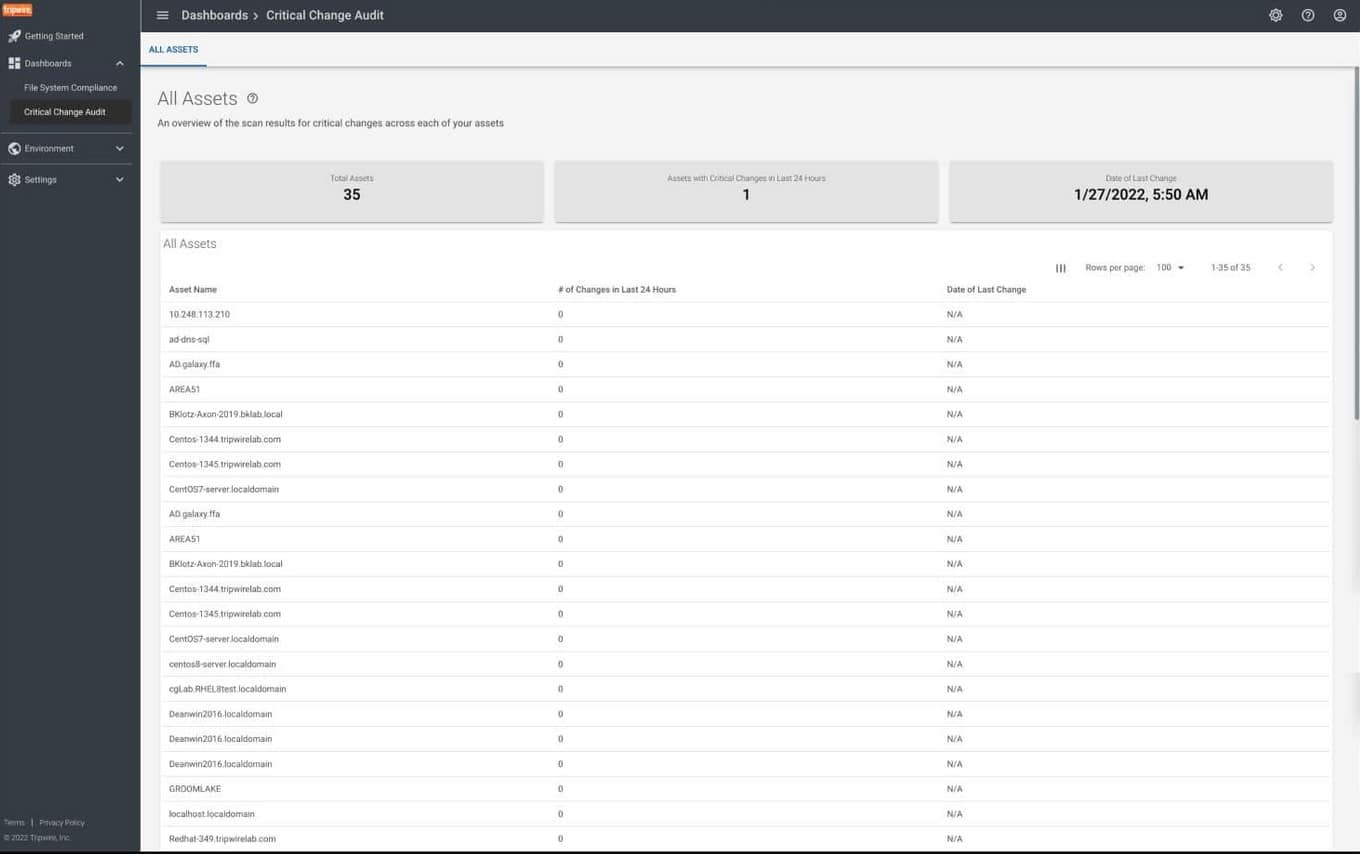
8. Tripwire
Tripwire is yet another example of an enterprise product. Its fame comes from its ability to detect intrusions, however, its FIM abilities are not to be underestimated. Its main appeal is its user-friendly UI as well as how well it works out of the box. It’ll provide you with a variety of easily readable graphs which show changes per platform, and will tell you if those changes were authorized or not. You can also filter through these based on a number of factors such as which user made them, what time it was, etc.
Main Features:
- It’ll show you all of the details about any changes made
- You’ll be able to set up a scoring system that reflects your risk margins
- It automatically reconciles the changes it detects through its process, differentiating good changes from awry ones.
- It comes fully functional out of the box
This FIM tool comes together with compliance parameters, so if you’re hunting for ISO, CIS, NIST, or other guidelines, this might be the tool for you.
Download: https://www.tripwire.com/solutions/file-integrity-and-change-monitoring/
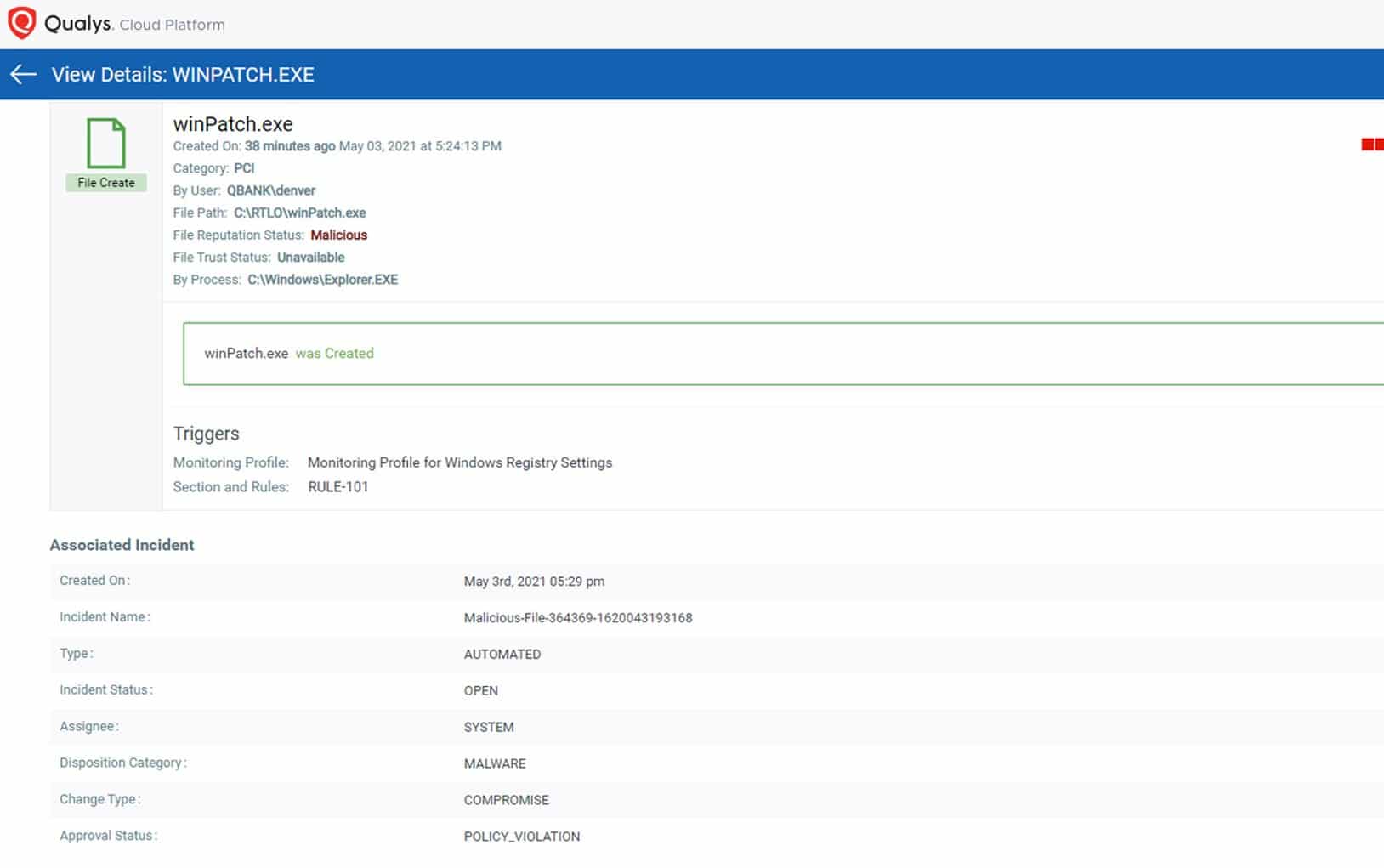
9. QualysGuard FIM
Qualys Cloud Agent is an efficient and robust FIM tool. It’ll swiftly take note of all file changes, and allow you to group up your files for notification purposes. This helps with finding simpler changes such as making files, renaming, or deleting them. One of its biggest perks is its cloud nature, as most businesses are no longer on the market for on-premise installations.
Main Features:
- Picking what to monitor can be a difficult task, Qualys automates this by having in-built out of the box profiles based on your industry.
- It comes with best practices and a variety of vendor-suggested guidelines, compliances, and PCI mandates
- It is easily scalable to a larger business
While the Qualys Cloud Agent is a quality tool, users have made complaints about the lack of customizability, as well as the UI’s ambiguity at times.
Download: https://www.qualys.com/apps/file-integrity-monitoring/
Who Can Benefit From FIM?
Pretty much all businesses should invest in FIM software. With that being said, certain industries make file integrity a top priority, and in these cases, FIM tools are almost mandatory:
- Highly Regulated Industries: Certain standards will require your business to have an FIM solution in order to pass them, such as HIPAA or Sarbanes-Oxley. The financial and medical industries are most affected by this, as are businesses that process credit cards.
- Industries Handling Sensitive Info: If your organization is handling sensitive information such as trade secrets, purchasing an FIM tool might be just what you need. While these cases don’t make it mandatory to do so, it can represent a large advantage over your competition, as well as help avoid scandals.
- All Businesses: It’s a common myth that only enterprises need FIM software. While it is true that they are in much direr of a need, small and medium businesses can benefit from it as well. With open-source options available on the market, there is hardly any reason not to have one.
Keep in mind that even if you’re only running a small or medium business, hacks are becoming more and more common, and preventing them might be all that stands between you and bankruptcy.
How To Choose The Best Tool
If you’re running a business with a vast array of crucial files, then you’ll want to go for the software with the highest integrity, regardless of cost. If you’re looking to centralize your data, and profit from quality FIM, then the Security Event Manager is your ideal choice. On the other hand, if you’re still skeptical about FIM, and do not find it mandatory, starting with a tool like OSSEC might be just what you need to change your mind.