When German programmer Tobias Frömel became a victim of Muhstik ransomware and was forced to pay 0.09 Bitcoin ($740 USD) to recover access to his files, he wasn’t going to sit back and be taken advantage of.
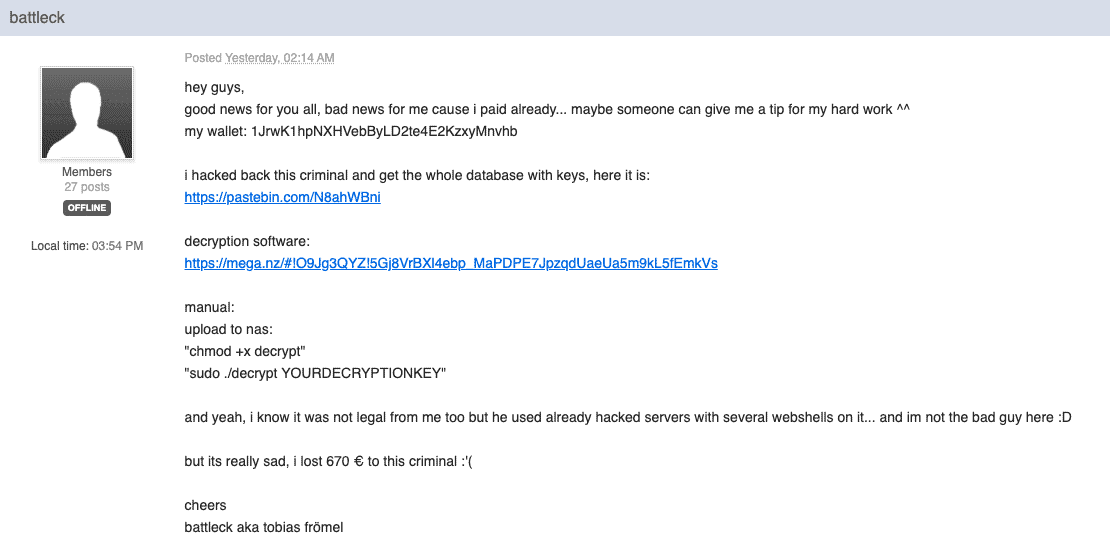
In a Bleeping Computer forum post on Oct. 7, Frömel revealed that he had hacked the attackers’ database, sharing almost 3,000 decryption keys and a free decryptor with fellow victims:
Illegal but Worth it:
Although what he did was technically illegal, Frömel wasn’t afraid to come out and share his success.
In revenge, he attacked their command and control server by retrieveing the unique Harware ID’s (HWID’s) and decryption keys for the 2,858 Muhstik victims stored in the attackers’ database.
Victims of Muhstik have confirmed that the HWID’s are accurate and that the decyptor Frömel shared on the Muhstick support and help forum actually works.
Furthermore, in an attempt to do some good–and deprive cybercriminals of income–Frömel has been seeking out Muhstik victims on Twitter and pointing them towards his decryption keys and instructions on how to recover their data.
Still a Growing Threat:
Even though Frömel “hacked back” against the Muhstik ransomware, there are still lots of similar ransomware out there.
Anti-virus firm Emsisoft released decryption software for victims running ARM-based QNAP devices.
Emsisoft also released a new free fix for WannaCryFake, a bitcoin-demanding ransomware.
With decryption software and new security measures being taken every day, Cointelegraph reported that ransomware attacks have still increased by 118% in the first quarter of 2019.