UFW stands for “Uncomplicated Firewall” is the default firewall tool for Debian based operating systems. It is an alternative program to iptables that simplifies the process of configuring and managing the firewall.
Generally, iptables is a very advanced tool with powerful functionality, but it’s syntax is very complex and difficult for beginners. While UFW provides user-friendly syntax that makes it easier to manage your firewall. UFW also provides a user-friendly front-end for managing iptables firewall rules.
UFW may be the appropriate solution for you are looking to secure your network easily.
In this tutorial, we will show you how to install and use UFW firewall on Linux.
Requirements
- A server running Ubuntu operating system.
- A root password is configured on your system.
Install UFW
By default, UFW is installed in most Ubuntu operating systems. If not installed, you can install it by running the following command:
apt-get install ufw -y
Once the installation is completed, you can check the status of UFW firewall with the following command:
ufw status
You should see the following output:
Status: inactive
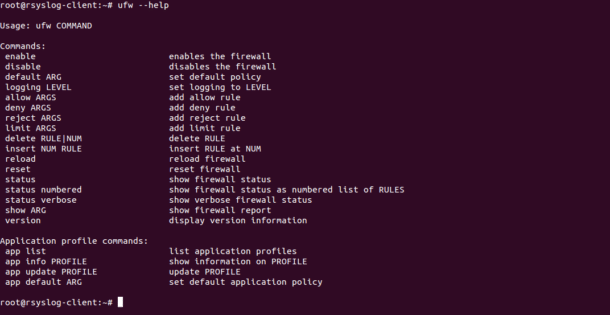
You can check all the options available with UFW using the following command:
ufw --help
You should see the following screen:
Configure UFW Default Policies
By default, UFW is configured to allow all outgoing connections and deny all incoming connections. Before started with your UFW firewall, set your UFW firewall rules back to the defaults. You can set the default policy with the following commands:
ufw default deny incoming
ufw default allow outgoing
Now, anyone trying to access your server can not be able to connect your server.
Next, you will need to activate the UFW firewall to apply the changes. Before activating the UFW firewall, it is recommended to allow incoming SSH connection to access your server from a remote location. You can allow incoming SSH connection with the following command:
ufw allow ssh
Or
ufw allow 22
If your SSH is configured to listen on a different port (2222 )then run the following command:
ufw allow 2222
Now, you can enable the UFW firewall using the following command:
ufw enable
Allow incoming Connections
There are several ways to allow incoming connections like, allow specific port, allow specific port range, allow specific IP address, allow specific subnet and allow specific network interface.
Allow Specific Port
By default UFW is configured to deny all incoming connections. So you will need to allow specific port as per your need.
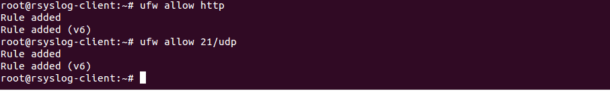
For example, to allow incoming HTTP connections run the following command:
ufw allow http
You can also specify port number instead service name as shown below:
ufw allow 80/tcp
To allow incoming connection on UDP port 21 run the following command:
ufw allow 21/udp
You can see a sample output of the above commands in the following screen:
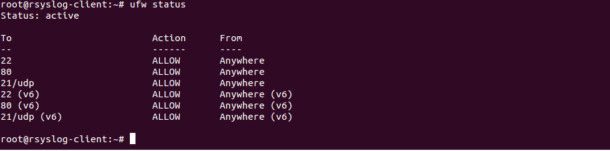
You can also check the status of UFW firewall with the following command:
ufw status
You should see the following screen:
Allow Specific Port Range
Instead of allowing single ports UFW also allows you to specify multiple port numbers in a single command. For example, you can allow incoming connections from ports 8000 to 9000 with the following command:
ufw allow 8000:9000/tcp
To allow UDP port range 8000 to 9000, run the following command:
ufw allow 8000:9000/udp
Allow Specific IP Address
UFW allows you to access all ports from a specific IP address. For example, if you want to allow all incoming connections from the IP address 192.168.0.100 run the following command:
ufw allow from 192.168.0.100
You can also allow access to specific port (8080) from the specific IP address (192.168.0.101).
ufw allow from 192.168.0.101 to any port 8080
Allow Specific Subnet
You can also allow incoming connections from a range of IP addresses. For example, to allow all incoming connections from the IP address 192.168.0.1 to 192.168.0.254 run the following command:
ufw allow from 192.168.0.0/24
You can also specify the destination port 8089 that the subnet 192.168.0.0/24 is allowed to connect to as shown below:
ufw allow from 192.168.0.0/24 to any port 8089
Allow Specific Network Interface
If you want to add firewall rules that only apply to a specific network interface (eth0). For example, allow all incoming connections to the network interface eth0 run the following command:
ufw allow in on eth0
You can allow access on a specific port 9000 only to specific interface eth0 by running the following command:
ufw allow in on eth0 to any port 9000
Deny incoming Connections
You can deny all incoming connections on port 80, 443 and 25 with the following command:
ufw deny 80/tcp
ufw deny 443/tcp
ufw deny 25/tcp
To deny all incoming connections from specific subnet, run the following command:
ufw deny from 192.168.1.0/24
To deny all incoming connections from specific IP address, run the following command:
ufw deny from 192.168.0.102
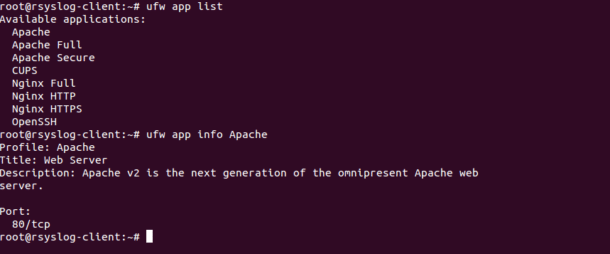
List Application Profile
By default, all application profile saved in the /etc/ufw/applications.d directory. You can list all application profile with the following command:
ufw app list
You should see the following output:
Available applications:
Apache
Apache Full
Apache Secure
CUPS
Nginx Full
Nginx HTTP
Nginx HTTPS
OpenSSH
You can also see the information about a specific application with the following command:
ufw app info Apache
You should see the following output:
Profile: Apache
Title: Web Server
Description: Apache v2 is the next generation of the omnipresent Apache web
server.
Port:
80/tcp
You can see a sample output of above commands in the following screen:
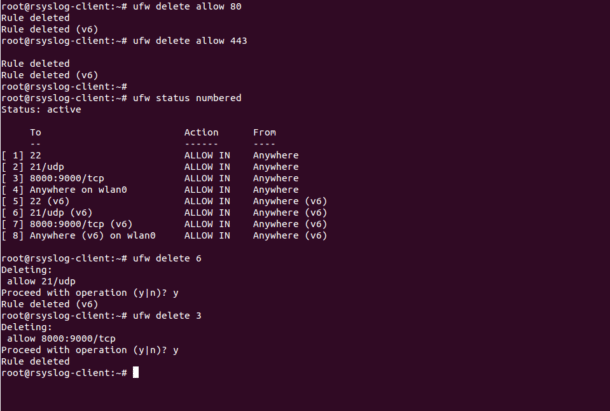
Delete UFW Rules
There are two ways you can delete UFW rules, with the actual rule and with rule numbers.
The first method to delete a rule by specifying the actual rule. For example, to delete a rule for port 80 and 443 run the following command:
ufw delete allow 80
ufw delete allow 443
The second method to delete a rule by specifying rule numbers. First, you will need to find the number of the rule you want to delete. You can list all the rules with numbers as shown below:
ufw status numbered
You should see the following output:
Status: active
To Action From
-- ------ ----
[ 1] 22 ALLOW IN Anywhere
[ 2] 21/udp ALLOW IN Anywhere
[ 3] 8000:9000/tcp ALLOW IN Anywhere
[ 4] Anywhere on wlan0 ALLOW IN Anywhere
[ 5] 22 (v6) ALLOW IN Anywhere (v6)
[ 6] 21/udp (v6) ALLOW IN Anywhere (v6)
[ 7] 8000:9000/tcp (v6) ALLOW IN Anywhere (v6)
[ 8] Anywhere (v6) on wlan0 ALLOW IN Anywhere (v6)
Now, delete the rule number 6 with the following command:
ufw delete 6
To delete the rule number 3, run the following command:
ufw delete 3
You can see the sample output of all commands in the following screen:
Enable UFW Logging
Enabling UFW logging is very useful to troubleshoot your firewall rules.
You can enable logging with the following command:
ufw logging on
You can also disable the UFW logging any time with the following command:
ufw logging off
By default, UFW logs are stored in the file /var/log/ufw.log. You can see it with the following command:
tail -f /var/log/ufw.log
Reset & Disable UFW
If you want to revert all of your changes that you have made with UFW, run the following command:
ufw reset
The above command will disable UFW and delete all active rules.
In some cases, you want to disable and deactivate all the rules. You can do it with the following command:
ufw disable
Conclusion
In the above tutorial, we learned how to install, configure and working with UFW firewall. I hope you have now enough knowledge to secure your system with the UFW.