When using Wireshark to monitor web traffic, you’ll find that a lot of the traffic is encrypted. Today, we’re looking at how you can decrypt SSL using Wireshark.
Most sites these days are using SSL or TLS (Transport Layer Security) encryption to make sure their users stay safe. Unfortunately, although encryption is good for you when browsing Reddit, it can be quite a hassle for network administrators.
About Wireshark And SSL
Wireshark
Wireshark is a well-known network traffic analysis tool. A lot of network administrators use it to help them with troubleshooting. The tool will take snapshots of frames, letting you sift through and analyze them individually. Often, it’s used in tandem with another network monitoring tool. Usually, one that provides higher complexity, but read about that in our last section!
Wireshark helps network admins take a closer look at the traffic going through their network; you can see inside the frames that make up each packet and take a look at the raw data behind them.
SSL
SSL or Secure Sockets Layer is an encryption protocol working on the Transport layer of the OSI model. This protocol uses multiple different encryption methods to ensure that data is secure when traveling through networks.
SSL has a successor, TLS or Transport Layer Security, that does its job better in most situations. So we’ll be using SSL to refer to both of these at once.
Why Does SSL Make Using Wireshark Harder?
SSL encrypts data traveling from network to network, which prevents the network administrator from looking at the data within each packet. With that being said, Wireshark can decrypt SSL so that you can look at the data again.
Taking Advantage of Pre-Master Keys
The easiest way to decrypt SSL using Wireshark is by taking advantage of pre-master keys.
The client generates a pre-master key and then uses the server to derive a master key, encrypting the traffic. This is today’s cryptography standard and is generally implemented through Diffe-Hellman key exchange.
You can set the browser up to log the pre-master key, which will then let Wireshark use it to decrypt SSL.
So, how do you do this?
- Set an environment variable from Advanced System Settings in Windows
- Double-click on the browser of your choice
- Set up Wireshark
- Start capturing and decrypting session keys
These four steps will allow you to decrypt SSL without needing to access the target server.
1. Setting An Environment Variable
You can set the environment variable you need by accessing Advanced System Settings. The variable in question is SSLKEYLOGFILE, and it has a path containing the storage location of the pre-master keys.
- Right-click on My Computer
- Go to “Properties,” opening the System menu
- Click on “Advanced System Settings”
- Go to the “Advanced” tab, and click “Environment Variables”
- Click on “New” in the User Variables section. If you’d like to log SSL keys for all platform users, you can create this variable in the System Variables section instead.
- Give it the following Variable Name: SSLKEYLOGFILE
- Within the “Variable Value” section, write the path to your log file. Alternatively, you can click the browse file button and simply pick one.
With that being said, if you’re creating an environment variable for the whole system, then you’ll need to use the right wildcards or have the file in a place accessible by all users. Occasionally, you might need to restart your device before the system registers the Environment Variable.
Setting An Environment Variable in Mac or Linux
Linux and Mac make it a bit harder to set up the SSLKEYLOGFILE environment variable. So we’ll have to use nano for it. On Linux systems, this variable will be stored in ~/bashrc. In case you’re using a Mac device, you should look in ~/.MacOSX/environment.
In Linux and Mac, you’ll need to set the SSLKEYLOGFILE environment variable using nano. In Linux, the variable is stored in ~/.bashrc. On the Mac, you’ll create the variable in the file ~/.MacOSX/environment
- On Linux, open up the terminal; on Mac, open up Launchpad and launch a terminal.
- Run the command nano ~/.bashrc on Linux or nano ~/.bash_profile on Mac
- Add a final line: “export SSLKEYLOGFILE=~/.ssl-key.log”
- Save your changes
- Close your terminal and then open it again. Write the “echo $SSLKEYLOGFILE” command to make sure you’ve set it right.
- You should see the path to your SSL pre-master key log on the screen. Make a note of this path as it’ll be helpful for you in the future.
This is all you need to do to set the variable, and now we can move on to further steps.
2. Look For The Log File In Your Browser
Before you start up Wireshark and get to decrypting SSL, you’ll need to ensure that your browser uses your log file.
First, you’ll want to visit a website that has SSL enabled. It doesn’t matter what website this is, as you just need to see one to make sure your log is being filled out correctly. Thankfully, since we’re using a pre-master key, we don’t need server access.
Once you’ve done that, you can check your log file to see if it has collected data. On Windows, you can use notepad or another text editor, while Linux and Mac have the command:
Cat ~/.ssl-log.key
Regardless of the operating system you’re using, and you should be getting a lot of incoherent data. Once you’ve ensured that your browser is using the pre-master key, then it’s time to move on to using Wireshark to decrypt SSL.
3. Decrypting SSL With Wireshark
When you get your browser to start logging the pre-master keys, you should begin configuring Wireshark to take advantage of the logs to decrypt SSL.
- Open up Wireshark
- Go into edit, then move into Preferences, opening the Preferences dialog.
- You’ll see various boxes and items, click Expand Protocols, and then find SSL, clicking on it.
- When a list of options of the SSL protocol pops up, you should see an entry for the pre-master secret log filename. Then, much like in the previous step, you can write the path or browse for a file.
- Once you’ve set the pre-master-secret log file’s name, press “Ok” and go back to Wireshark.
Capturing A Session & Decrypting
Finally, we’ll be looking at how you can capture a test session to ensure that Wireshark correctly decrypts SSL.
- Set up an unfiltered capture session
- Minimize the session and open your browser of choice
- Go to a site that uses SSL to secure itself to get enough data
- Click any frame that has encrypted data.
- Switch to the Packet byte view, and look at the sections underneath it. There should be an entry for decrypted SSL data
- If your screen looks like the page is gibberish, and you aren’t seeing HTML, it’s likely to be caused by the site using GZIP compression
- In these cases, you can click the “Uncompressed Entity” tab to see the source code for the site. This will get around GZIP compression and let you know the HTML properly
Using this method, you’ll be able to decrypt any transmissions using a pre-master secret or private key. That means all transmissions with PFE using Diffe-Hellman or similar key exchanges will be easily decrypted.
There are other methods to decrypt SSL with Wireshark; however, they’ve mostly been made obsolete by pre-master secret key decryption.
Let’s Use A RSA Key To Do It
Wireshark has a field where you can use it to upload your RSA key(or multitudes of them) and take advantage of them to decrypt SSL. With that being said, RSA decryption has been made pretty much obsolete.
The reason this happened is that sessions that use Diffie-Hellman don’t use their RSA keys directly anymore. Instead, they generally make a one-use key stored in the RAM. Then, they encrypt their data using that key on the disk.
If you used RSA key decryption to decrypt traffic and it doesn’t work anymore, you can check if the target server is still using Diffie-Hellman by using SSL logging.
To set this up, you’ll need to go to “Edit” from Wireshark’s toolbar and go to Preferences. Like in the past steps, you’ll want to find “Protocols” and go to SSL. There, you’ll be able to browse your device for an SSL log.
Once you’ve chosen your location, all of the SSL you interact with will be logged in that file.
Next, you’ll want to capture a session and look at your logs. You should be looking for the specific frame in the TLS handshake that happened. You’ll often find a DHE entry within the cipher string, meaning Diffie-Hellman key exchanges are working correctly.
If you can find a line saying “Cannot find the master secret,” that means that you won’t be able to decrypt the data by using an RSA key. The best way for you to resolve this is by using the pre-master way of decrypting outlined above.
Wireshark SSL Decryption FAQ
What Does A 2-Way SSL Handshake Do?
A 2-way SSL handshake makes sure to authenticate both the server and the client. The steps carried out in this process are as follows:
- Client Greeting: A client sends a transmission containing the supported cipher suites and TLS versions to the target server.
- Server Greeting: The server sends a transmission to the client; the transmission has a link to the target server’s public certificate and a request for the client to provide one.
- A browser validates or invalidates the server certificate. If it’s verified, the browser then sends its certificate.
- The target server validates or invalidates the browser’s certificate. If it validates it, the transmissions continue both ways.
Can You Decrypt Passively Sniffed SSL?
Although you can indeed decrypt passively sniffed SSL, you’ll need the right RSA key to do so. You can gain this through standard methods and simply acquire permission, or a “man in the middle” strategy could be employed to get it indirectly.
What Should I Do To Read TLS Packets?
If you’re using Wireshark to read TLS packets, this is how you do it:
- Set up a packet capture session
- From the top menu bar, go to Edit, then select “Preferences”
- Expand Preferences and scroll down until you find “SSL,” then click on it
- Write the name of a file and pick a location for the SSL debug file
- Go to the RSA keys list and click “Edit”
- Press “New”
- Fill out the information Wireshark asks from you
- Press “Ok”
- The information at the bottom of your main Wireshark page will then show you the packet’s content.
Best Wireshark Alternatives
Wireshark is great and all, but sometimes firms need something with just a little bit more oomph to give them better monitoring capabilities. Thankfully, there’s a lot of Wireshark alternatives that do an excellent job at surpassing it.
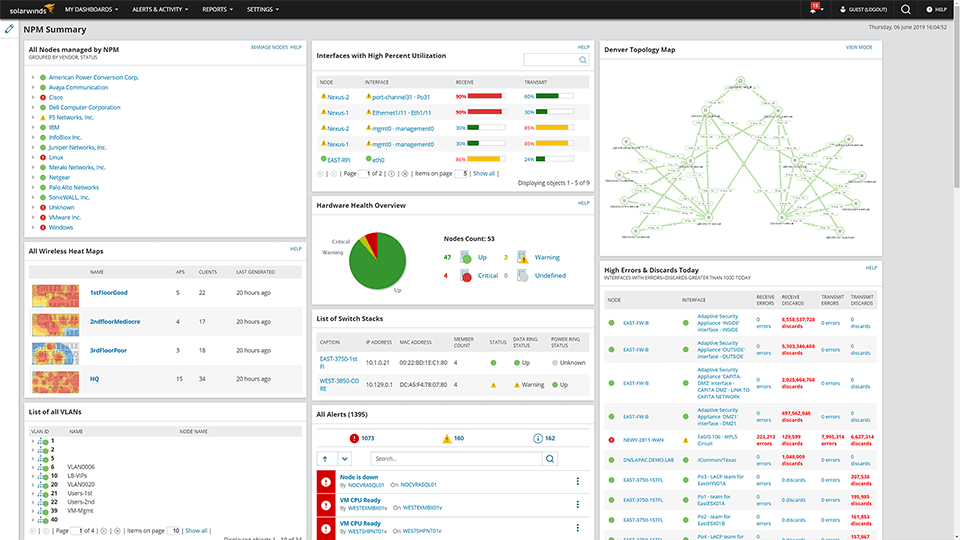
1. SolarWinds Network Performance Monitor – FREE TRIAL
The SolarWinds Network Performance Monitor is the premiere network monitoring software on the market. The SNPM will discover all of the devices on your network and create a map of them within a single hour.
It’s straightforward to customize how you view your web-based applications using the SNMP. For example, you can create different dashboards measuring the performance of your network.
Main Features:
- The SNPM can monitor multiple vendors at once
- Look at the whole picture- the SNPM gives you complete visibility of your network
- The NetPath and PerfStack functionalities make troubleshooting a breeze
- Extremely scalable
- Decrypts SSL almost automatically if you need it to
Pricing:
All in all, if you’ve got the $2,675 that it takes for a year of SNPM usage, it’s well worth it. It offers an almost strictly better experience than Wireshark, with many more functionalities to improve your network monitoring. The SolarWinds Network Performance Monitor comes with a 30-day free trial.
Download the 30-day FREE Trial
https://www.solarwinds.com/network-performance-monitor
2. Paessler PRTG
The Paessler PRTG monitor excels at monitoring your IT infrastructure from a distance. One of its main selling points is how good it is at monitoring multiple networks at once.
Main Features:
- Fully-fledged web interface based entirely on AJAX employing the highest security standards
- SSL-secured access both on-prem and remote
- Excellent visualization capabilities help you adapt to issues in your network on the fly
- Multi-network monitoring
The Paessler PRTG is paid on a sensor-based model, letting you only pay for the functionalities you need. With that being said, SSL decryption is a tiny bit more complex than on Wireshark.
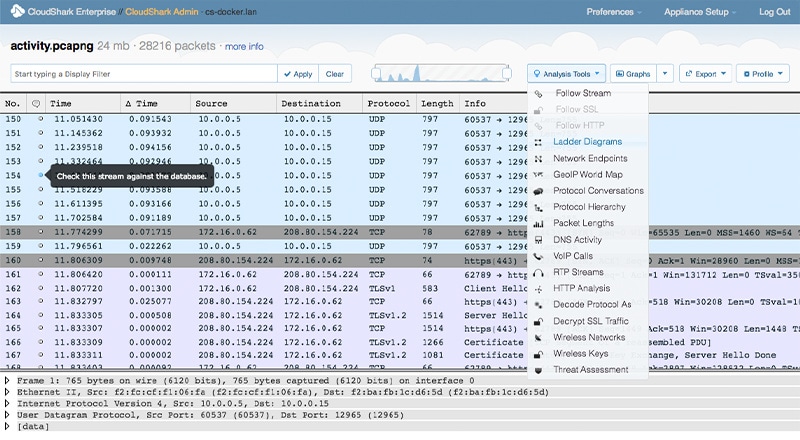
3. CloudShark
CloudShark tries its best to make analyzing and sharing packet captures as easy as possible. It aims to be quicker and more efficient than Wireshark at solving some of its biggest problems.
- The drag-and-drop interface makes it incredibly simple to use
- You can upload your API key
- It can act as a storage space for the files you generate using it
- You can gather advanced analysis data from your device without any additional software
- Instant linking so you can share your reports with the team.
- Entirely web-based
Cloud Shark boasts a 90-day free trial! However, it is pretty pricey at $4500 a year.
Closing Words
Wireshark makes the SSL decryption process as simple as it can get. Unfortunately, cryptography tends to get more and more complex with time. With protocols getting more and more secure, you must have a way to analyze the data coming in correctly.
Wireshark lets you analyze and decrypt all of your SSL traffic with ease, making the whole monitoring process a lot easier. With that being said, it has its downsides. Wireshark isn’t very scalable, so if you’re looking for a more long-term solution, you might want to change to one of its alternatives.
Did we forget your favorite Wireshark alternative?
How do you prefer to decrypt SSL using Wireshark?
Let us know in the comments below!