We spend lots of time on a daily basis surfing the web for information, news, entertainment, shopping, and a host of other activities including maintaining contact with friends and family.
These common websites are part of the Visible Web or Surface Web.
However, there exists a whole different world on the web, that most people are unaware of and this is known as The Dark Web.
The dark web (or dark net) is the term used to refer to the part of the internet that can’t be found using conventional search engines and requires anonymizing browsers such as Tor to be accessed.
While the dark web offers a considerably higher level of privacy and secrecy with standard web services, a lot of illegal activities also take place here, such as exchange of stolen credentials or vending illicit drugs.
In 2016, Daniel Moore and Thomas Rid carried out a study in an attempt to find out the extent of illegal activity carried out on the dark web.
Out of the 5,205 sites they identified, nearly 48% were inactive and had no content.
On the other hand, half of the sites that appeared to be active were associated with a wide range of illicit activities.
423 sites were associated with trading or manufacturing illegal drugs, including illegally acquired prescription drugs.
327 sites facilitated financial crimes like counterfeiting, money laundering, or merchandise of stolen accounts and credit cards.
They also found 140 sites associated with extremist ideologies or terrorist attacks, 122 sites containing child or animal pornography including materials obtained without participants’ consent.
Among the sites they found a small number of hacking tools and marketplaces, a couple of sites trading weapons, and 17 sites claiming to offer hit-men for hire or facilitating violence in other ways 4.
In a separate study done in 2019 – Into the Web of Profit, carried out by Dr. Michael McGuires14 at the University of Surrey, the number of dark web listings that could potentially harm an enterprise has increased by 20% since 2016.
He further asserted that 60% of all listings (excluding drug sites), have the potential to harm enterprises.
Some very common activities that take place on the dark web include buying of credit card details, stolen subscription credentials, drugs, guns, counterfeit money, hacked Netflix accounts and software that grants you unauthorized access into other people’s computers.
It must be stated at this point that not everything on the dark web is actually “dark”.
There is also a legitimate side to it as well as some benefits.
As stated earlier, the dark web provides a high level of user privacy and this can really come in handy in certain situations.
For instance, it provides a platform for journalists who are trying to evade government censorship to share info about happenings in their country.
Whistle-blowers can also leverage on the dark web to find allies who can share their confidential information to the general public 5.
A typical example of one benefit of the dark web is the case of the COVID-19 outbreak in Wuhan, China.
Initially, information about the outreach was censored, and doctors were not permitted to speak out.
Concerned about the potential spread of the virus, some Chinese “netizens” took to the dark web to spread the word, knowing it would be nearly impossible for the leaked information to be traced by their government 5.
Deep web vs. Dark web: Same or different?
“Deep web” and “Dark web” are often used interchangeably but they are really not the same.
The deep web refers to the parts of the internet not indexed by and, therefore, inaccessible through search engines like Google.
Anything behind a paywall or requiring sign-in credentials (such as your password protected email account) can be classified as Deep web content.
Deep web content also includes content that its owners have barred web crawlers from indexing.
Some of the things that make up the deep web include web mail, online banking, web forums that require registration, restricted social media pages, paid services protected by paywalls such as online magazines and newspapers7.
The deep web is estimated to make up about 96% to 99% of the internet.
The dark web, on the other hand, is a subset of the deep web – only a small fraction (0.01%) 6, and requires a specific browser – Tor – to access.
It is also characterized by the use of encryption software that makes users and user locations anonymous.
Risky Tools and Services on the Dark Web
According to the Into the Web of Profit study by Dr. Michael McGuire, there are essentially 12 categories of tools and services that portend risk such as network breach or data compromise.
These include:
- Credentials
- Phishing
- Refunds
- Customer data
- Access, including Remote Access Trojans (RATs), Keyloggers and Exploits
- Support services such as tutorials
- Financial data
- Intellectual property/trade secrets
- Operational data
- Infection or attacks, including malware, distributed denial of service (DDoS) and botnets
- Espionage, including services, customization and targeting
- Other emerging threats
In each case, there are three risk variables which are listed below with examples:
- Enterprise Devaluation
Undermining brand trust, reputational damage or losing ground to a competitor - Enterprise Disruption
DDoS attacks or other malicious software that affects business operations - Enterprise Defrauding
Espionage or IP theft leading to direct financial losses or impairing a company’s competitive abilities.
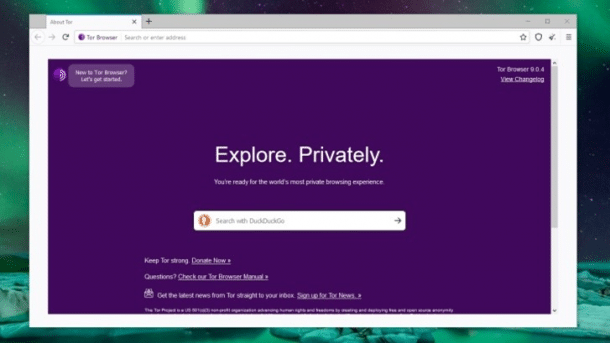
Accessing the Dark Web
Considering the anonymity and privacy of the dark web, it cannot be accessed using normal web browsers like Chrome, Edge or Firefox.
A special anonymizing browser called “Tor” is used to access the dark web.
TOR is an acronym for “The Onion Router”. It is an open source privacy network that permits users to browse the internet anonymously.
Before it was made available to the public, it was originally developed and used solely by the US Navy for censoring government communications 9.
The Tor browser makes use of what is known as the “onion routing technique” for transmitting data.
It achieves anonymity by routing web page requests through thousands of proxy servers run by volunteers all over the world.
This makes it nearly impossible to identify or trace IP addresses.
What’s the magic?
So here’s how the Tor browser works…
Normally, Internet service providers (ISPs) assign IP addresses to each computer that accesses the internet.
When a user tries to access a particular web page, eg. google.com, the network retrieves the IP address linked to the requested domain and sends back to the user’s assigned IP address as soon as access is authorized.
However, with Tor browser, the Tor network does not pass the request from the user directly to the final destination.
In this case, the request is first bounced off a random number of IP addresses from other users (encrypting the information afresh each time).
The last node (IP address) that the information is routed through before hitting the final destination is known as the exit node.
Before the request is relayed from the exit node to the final destination it is first decrypted.
The requested web page grants access to the exit node, believing that the request originated from it.
The exit node then repeats the encryption process in reverse order until it gets to the originating computer/user.
Dark web sites
Dark websites look like regular websites but there are some key differences.
- Suffix:
They end in .onion, in contrast to .com, .net or .org on the surface web. This special suffix ensures that only browsers with the appropriate proxy (like Tor) are able to access these sites. - Naming Structure:
URLs of dark websites are usually nonsensical and appear like a string of meaningless characters making it impossible to remember (e.g. https://3g2upl4pq6kufc4m.onion/) - Life Cycle:
Dark websites are often short-lived as many of them are set up by scammers constantly on the move in order to avoid being discovered by their victims. Ecommerce sites can suddenly be taken down when their owners decide to disappear with money obtained from customers. - Vulnerability:
The anonymous nature of the Tor network makes it susceptible to Distributed Denial of Service (DDoS) attack. As a result of this, site addresses are constantly changed, maintaining a very dynamic environment and leaving a lot of search material outdated.
Dark web search engines
Owing to the nature of the dark web, it is difficult for search engines like Google to work here.
However, it is still possible to navigate through the dark web using search engines and directories but you’ve got to know where to look.
Outlined below are some of the sites that can definitely give you a head start:
- Hidden Wiki:
The hidden wiki is a dark web Wikipedia containing a compendium of different websites on the dark web. It provides information and links to a myriad of interesting topics to read. Illegal websites are also found on the hidden wiki, and there are quite a number of spin-offs out there like “The official Hidden Wiki” or “The Uncensored Hidden Wiki”. It’s best to avoid these sites but if you must visit them, you’ve got to tread with caution. The hidden wiki can be accessed using the following URL on Tor browser of course: http://zqktlwiuavvvqqt4ybvgvi7tyo4hjl5xgfuvpdf6otjiycgwqbym2qad.onion/wiki/index.php/Main_Page - DuckDuckGo:
This search engine, also available on the surface web can be used in the dark web as well because it shows .onion websites. DuckDuckGo does not collect or share personal information and is ideal for maintaining complete anonymity. Here’s the link to the dark web version of DuckDuckGo: https://3g2upl4pq6kufc4m.onion/ - SearX:
This is another search engine that works both on the dark web and the surface web. The advantage of this search engine is that it gives you the chance to be very detailed in your search query (just like google). You can search for files, images, music, videos, news, maps, social media posts, and a lot more. Here’s the link: http://ulrn6sryqaifefld.onion/ - Candle:
This site is meant to function just like google on the dark web. However, because the dark web is not designed to be organized and indexed, this search engine is not as useful. Basically, you can view the “candle” as a small candle in a long hallway that does not let you see beyond your nose. You must be vigilant when using it. Here’s the link: http://gjobqjj7wyczbqie.onion - Not Evil:
This search engine hosts links to hidden illegal services. If you search for “cocaine”, for instance, it will find links to associated online markets, guides, or referral sites. Not Evil also hosts a chat service that gives all members the privilege to create a new topic. Members of these chat services can include hackers, scammers, and even law enforcement officials attempting to catch law breakers. However, most of the content here is spam. Here’s the link to access the Not Evil search engine: http://hss3uro2hsxfogfq.onion/
Business transactions on the Dark Web
A wide range of goods and services are sold on the dark web.
These include: Credit Card Information, Research Data, Trade Secrets & Formulae, Blueprints & Security Plans of buildings, networks etc., Medical Records, Financial Records, Intelligence Reports and Government Secrets to mention but a few11.
Crypto currencies such as Bitcoin are a major factor, influencing the growth of the dark web.
Bitcoin enables two parties to carry out a trusted transaction anonymously, and because of this nearly all eCommerce sites on the dark web carry out transactions using bitcoin or some other cryptocurrency.
This, however, does not guarantee safety in doing business here.
One can still easily get scammed or robbed because of the inherent anonymity.
Commercial sites on the dark web operate just like any other e-commerce site on the surface web.
They have features like ratings/reviews, shopping carts and discussion forums.
However, there are salient dissimilarities.
Take quality control for instance.
Given that buyers and sellers are fully anonymous, the credibility of ratings is questionable.
Ratings can be manipulated easily, and even vendors with long track records have been identified to suddenly disappear with their customers’ funds, only to set up another shop at a later time using a different alias.
Even when a transaction is completed, there is no guarantee that the purchased goods will arrive.
In some cases where goods are transferred across countries, suspicious packages may be confiscated by customs officials.
There have also been reports of buyers who were arrested or prosecuted for attempted purchases.
Is The Dark Web Illegal?
The simple answer is “No”. The dark web in itself is not illegal, but a lot of the activities that go on there are illegal.
There are sites for vending illegal drugs and others where you can purchase weapons and firearms illegally.
There are also child pornography sites.
On the flip side, there are also a whole lot of sites that do not violate any laws.
For instance, you can find many forums, blogs, and social media sites that cover topics like politics and sports which are not illegal.
The Tor network began as an anonymous communications channel, and still serves the purpose of helping people communicate in environments that are antagonistic to free speech.
People use it in places where internet access is criminalized.
On Intel Exchange (A dark website), discussions about current events can be conducted anonymously.
There are numerous whistle-blower sites, including a dark web version of Wikileaks.
Pirate Bay, a BitTorrent site that law enforcement officials have repeatedly shut down, works well on the dark web.
There is even a dark web version of Facebook.
Many legitimate web companies are beginning to register their presence on the dark web.
Law enforcement agencies constantly monitor the dark web looking for stolen data from recent security breaches that may help them trail perpetrators.
Some media organizations monitor whistle-blower sites for news, as well.
Staying ahead of Hackers Underground
Cybersecurity professionals constantly put themselves into the minds of Hackers.
By thinking like the cyber-criminals, they are able to fight crime and stay one step ahead.
Hackers make use of the dark web to access and steal credit card details and other personal information from people.
Banks using old operating systems like Windows 95 and Windows XP are vulnerable to cyber-attacks since technology companies constantly launch newer versions of these software and stop supporting obsolete ones.
The cyber-criminals cash in on this loophole by simply finding a weak entry point.
In order to analyze a bank’s ATM system running on legacy software, an Ethical Hacker can devise a plan to find weak spots.
These professionals often chat with other hackers on the Dark Web, and use this medium to learn from their past activities.
The good thing here is that the Tor software and .onion sites ensure that these conversations remain untraceable.
Also, officers specializing in Narcotics use the Dark Web to identify how and where drug trafficking activities take place.
They then disguise themselves as smugglers looking to sell a new high-end drug or carry out money laundering via international banks.
The undetectable nature of Tor gives the police better tools for carrying out investigations12.
So here’s the catch: If you can stomach the horrible performance, volatile accessibility, and possible shock factor of the dark web, it’s worth the try.
Nonetheless, you should avoid buying anything there.
Protecting Your Organization from Dark Web Activities
With the proliferation of hackers and the growing use of the dark web, it is becoming increasingly difficult for organizations to safeguard their credentials from appearing on the dark web, where they could be exchanged or traded for malicious activities.
ManageEngine log360 is a SIEM tool that comes with a specialized dark web monitoring module. As the name suggests, this module provides visibility into breaches that led to the availability of your credentials on the dark web. It continuously monitors the dark web to check if any of your sensitive information as leaked to it.
More importantly, it sends instant alerts as soon as it detects any information, so you can take the necessary steps to mitigate the damage. With this tool, you can limit damage due to leaked data.
Try this tool with a 30-day free trial.
References:
- https://us.norton.com/internetsecurity-emerging-threats-what-is-the-deep-dark-web-30sectech.html
- https://en.wikipedia.org/wiki/Dark_web
- https://www.investopedia.com/terms/d/dark-web.asp
- https://home.sophos.com/en-us/security-news/2019/dark-web.aspx
- https://www.peraton.com/five-things-to-know-about-the-dark-web/#:~:text=There%20are%20some%20benefits%20to,is%20happening%20in%20their%20country.
- https://www.britannica.com/story/whats-the-difference-between-the-deep-web-and-the-dark-web
- https://en.wikipedia.org/wiki/Deep_web
- https://www.investopedia.com/terms/t/tor.asp#:~:text=Tor%2C%20short%20for%20’The%20Onion,made%20available%20to%20the%20public.
- https://www.investopedia.com/terms/t/tor.asp#:~:text=Tor%2C%20short%20for%20’The%20Onion,made%20available%20to%20the%20public.
- https://vpnoverview.com/privacy/anonymous-browsing/dark-web-websites-worth-visiting/
- https://www.idagent.com/blog/what-sells-in-dark-web-markets-in-2020/
- https://cybersecurity.miami.edu/the-dark-web-its-secrets-revealed/
- https://www.csoonline.com/article/3249765/what-is-the-dark-web-how-to-access-it-and-what-youll-find.html
- https://threatresearch.ext.hp.com/study-explores-dark-net-enterprise-risk/