CSPM tools are a powerful asset in any cloud security endeavor. They will help ensure all of your cloud data is kept secure and find misconfigurations if any occur. Since misconfigurations have played a part in a majority of data breaches in the past few years, CSPM tools have become practically mandatory for cloud-oriented businesses.
Most of these tools will help you find risks, resolve issues, fix misconfigurations, and aid with complying with regulations. However, they’re not all made equal. In our testing, Datadog has proven itself supreme with its modular approach to CSPM and wide variety of advanced features. However, the best CSPM tool for your business will always depend on your needs.
Here is our list of the best CSPM tools on the market today:
- ManageEngine Log360 Cloud – EDITOR’S CHOICE A cloud-native platform that provides detailed insights into your CSPM and identifies known and zero-day exploits. It also provides the data you need to prevent/remediate these attacks. It helps with compliance as well. Start a 30-day free trial.
- Datadog Integrates seamlessly with the rest of the Datadog ecosystem, and provides cutting-edge features in an intuitive package. Datadog supports over 500 different integrations and will cover all of your cloud security posture management needs. It’s also quite simple to use and deploys in a matter of minutes.
- Aikido The CSPM in this platform is an assurance service for DevOps teams and ensures that new applications aren’t installed on top of insecure cloud platforms and services.
- CrowdStrike Falcon Horizon CSPM A tool that provides real-time monitoring seamlessly integrates with countless SIEM tools and provides over 50 IOA detections.
- CloudGuard Posture Management A CSPM tool with excellent visualization features and Automated regulation compliance and governance.
- BMC Helix Cloud Security A tool with dependency mapping features and superb reporting capabilities.
- Trend Micro Hybrid Cloud Security Solution that provides a holistic monitoring experience and boasts automated deployment and discovery features
- Lacework An innovative CSPM solution that relies on machine learning to create more sophisticated features. Lacework also features behavioral analysis capabilities.
- Prisma Cloud An advanced, enterprise-focused CSPM tool with full-stack runtime protection capabilities, IaC template scanning, and container image scanning.
- Threat Stack A modern, customizable tool that focuses on threat detection and neutralization with machine learning capabilities.
The Best CSPM Tools
As technology advances, more and more companies are relying on cloud-based tools for their day-to-day operations. Cloud technologies’ ability to connect to hundreds of networks daily makes it powerful, however, it also causes a variety of security challenges. CSPM tools are therefore tasked with helping businesses with assessing risks, reacting to security threats, and ensuring regulatory compliance. Today, we’ll be going over the best CSPM tools available on the market.
1. ManageEngine Log360 Cloud – FREE TRIAL
ManageEngine Log360 Cloud is an advanced SIEM tool that can help you stay on top of vulnerabilities and security issues in your cloud environment. Its cloud-native architecture is flexible and scalable to meet your growing needs, while its coverage can detect most attacks before they impact your operations.
Key Features:
- Streamlines log collection and storage, and correlates them for insights.
- Gathers feed from threat intelligence databases to help you thwart the latest and emerging attacks.
- Offers advanced search and filter options to help you find what you need.
- Meets the compliance requirements of different standards.
- Sends real-time alerts for anomalous issues or risky behavior.
- Enables the creation of custom anomaly rules.
- Manages audit trails.
Why do we recommend it?
We recommend this tool because of its extensive coverage of potential threats that can impact cloud environments. Its ability to correlate data from multiple sources and provide deep insights into threats and their possible root causes can help IT administrators to proactively prevent these attacks.
Moreover, it generates audit trails and reports to meet compliance requirements. Its dedicated dashboards help understand the security and compliance gaps, so they can be addressed right away.
We also like the way this tool focuses on risky user behavior and AD-related threat identification, like identity threats and credential abuses. Together, all these features can better safeguard your cloud environments.
Who is it recommended for?
It is recommended for organizations that use cloud environments and applications. It is also particularly useful for organizations that have to meet strict security and compliance standards. This tool’s dashboards can enable network engineers and security teams to quickly identify and fix the root causes of issues.
EDITOR'S CHOICE
ManageEngine Log360 Cloud wins the best CSPM tool award from our editors for its comprehensive approach to security and its detailed coverage of the different threats that can impact cloud environments. Its real-time alerts, user-friendly dashboard, extensive audit trails, and prebuilt reporting templates come in handy for troubleshooting issues before they disrupt operations. Also, its focus on meeting the compliance requirements is notable. Due to these reasons, Log360 Cloud is at the top of our list.
Download: Start a 30-day FREE trial
Official Site: https://www.manageengine.com/cloud-siem/index-new.html
OS: Cloud
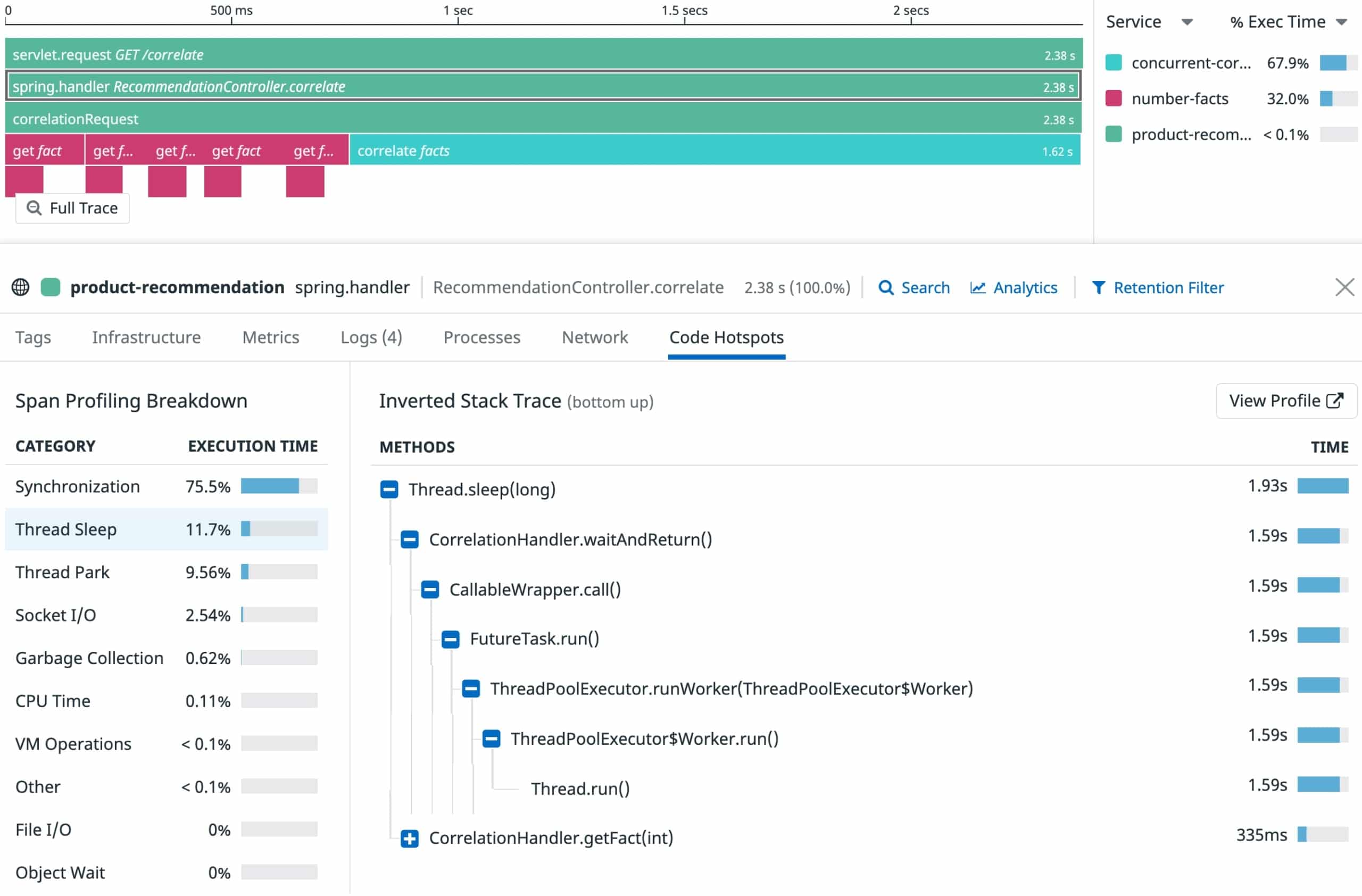
2. Datadog
Datadog is a big name in the world of network security. The company provides firms with a variety of tools to help them ensure they’ve got proper visibility of their infrastructure. Datadog is modular software, and the CSPM module is nothing short of fantastic.
Key Features:
- Continuously scans your entire infrastructure.
- Rapid installation.
- Provides real-time visibility and monitoring capabilities.
- Data aggregation features.
- Supports over 500 different integrations.
- Robust alerts system.
- Extremely scalable.
Why do we recommend it?
In our comprehensive testing of Datadog’s CSPM module, it proved to be a standout choice, seamlessly integrating with the Datadog ecosystem and offering cutting-edge features in an intuitive package. We extensively tested its continuous scanning capabilities, providing real-time visibility and monitoring across our entire infrastructure, including hosts, accounts, and containers. Datadog’s robust alert system and scalability addressed our need for rapid threat detection, ensuring a security posture score evaluation for proactive security measures. We used it for efficient identification and resolution of misconfigurations, a common cause of data breaches in cloud infrastructures.
Datadog provides continuous monitoring and scanning of all of your hosts, accounts, containers, and overall infrastructure performance. If you’re already using a Datadog tool and have the Datadog Agent installed, you won’t need to install any additional agents for the CSPM module.
Datadog continuously scans all of your configurations and provides full visibility into them. Since misconfigurations are one of the leading causes of data breaches in cloud infrastructures, it’s extremely helpful to have a tool that will alert you when something is amiss.
Datadog helps you scan your infrastructure for any hidden or incoming threats within your cloud instances or containers. Datadog is also great for companies that rely on a variety of different technologies as it supports over 500 different integrations.
Another perk of the tool is that it’s fairly easy to start using(although some advanced features are a bit harder to grasp) and installation only takes a few minutes.
Who is it recommended for?
Datadog is recommended for businesses seeking a modular and user-friendly CSPM tool with extensive integrations. Its continuous scanning and real-time visibility make it suitable for those prioritizing rapid threat detection and response. The tool caters to various sectors, supporting over 500 integrations and accommodating diverse technologies. Datadog is an ideal choice for businesses that value a seamless and quick deployment process, providing comprehensive cloud security posture management.
Whether you’re dealing with misconfigurations or need real-time visibility, Datadog offers a scalable solution for effective cloud security management.
The tool offers a free, 14-day trial.
3. Aikido
Aikido is an application security testing service that includes a CSPM. The cloud vulnerability scanning system is intended for use as part of the development and release pipeline for new Web applications and SaaS packages.
Key Features:
- Application security testing
- Examines Infrastructure-as-code, containers, and Kubernetes
- Provides a severity score
- Deduplicates alerts for errors with the same cause
- Cloud account configuration checks
- Integrates with CloudSPloit and AWS Inspector
- Looks for outdated runtimes within containers
Aikido provides security checks at all points of the development and release of a new Web application or SaaS package. The platform includes a software composition analysis (SCA) service that examines the third-party components that designers want to include in the new code. It implements both dynamic application security testing (DAST) and static application security testing (SAST) to examine newly developed code. It can be set up through a repository integration to operate as a continuous tester in a CI/CD pipeline.
The CSPM is part of an infrastructure assurance phase that would take place just before an assembled application is released. Once the application code has been verified as secure, it needs to be tested in a sandbox environment that completely mimics the intended conditions for the application’s hosting and invocation.
The CSPM partners with Infrastructure-as-Code assessments, container scanning, and Kubernetes checks. The cloud system on which the application will be run when live is assembled for suite testing. This looks for secret disclosure and possible problems with the passing of unprotected data between modules. It also checks that outsiders can’t break into the application through the supporting environment.
The Aikido service partners with CloudSploit and AWS Inspector to extract responses to test data from the intended platform. It also examines the access rights manager to look for loose permissions or user group definitions.
There are four plans available for the Aikido platform and they all include the CSPM. The main difference between the plans is the capacity of each of the facilities within. Even the Free edition provides all of the utilities of the paid plans. You can assess the Aikido platform on a free trial.
4. CrowdStrike Falcon Horizon CSPM
The CrowdStrike Falcon Horizon is an excellent choice for enterprises and SMBs alike. It provides a quick and lightweight CSPM experience while ensuring that you’re protected from misconfigurations and external threats.
Key Features:
- Real-time monitoring.
- Seamless integration with SIEM tools.
- Identifies and monitors data breaches.
- Over 50 IOA detections.
- Finds and automatically eliminates compliance violations.
- Useful suggestions for improving the cloud security posture.
Why do we recommend it?
During our evaluations, CrowdStrike Falcon Horizon CSPM emerged as a top choice for enterprises and SMBs, offering real-time monitoring and seamless integration with numerous SIEM tools. We extensively tested its capabilities, including over 50 IOA detections and compliance violation alerts. The tool’s quick and lightweight CSPM experience addressed our need for efficient protection against misconfigurations and external threats. It provided valuable insights into our security posture, and it helped us with the immediate identification and elimination of compliance violations.
The CrowdStrike Falcon also provides data regulation compliance assistance. It’ll immediately alert you if it finds any compliance violations. The tool also provides insights into your overall security posture. In addition to this, it monitors the APIs you use in your infrastructure in case malicious actors try to use them as an attack vector. The tool’s API can also allow your team to connect to a variety of different security tools.
The tool seamlessly integrates with SIEM solutions and provides real-time insights into your infrastructure. It’ll also give you suggestions on how you can improve your overall cloud security posture. With over 50 IOA detections and endpoint detection capabilities, the CrowdStrike Falcon Horizon is one of the most flexible CSPM tools on the market today.
Who is it recommended for?
CrowdStrike Falcon Horizon CSPM is recommended for businesses prioritizing real-time monitoring, lightweight CSPM experiences, and seamless integration with SIEM tools. Its over 50 IOA detections and compliance violation alerts make it suitable for enterprises and SMBs aiming for comprehensive threat detection and compliance management. The tool’s flexibility in monitoring APIs and providing actionable suggestions for improving security posture caters to diverse sectors, making it a valuable choice for businesses of varying sizes.
Whether you’re focused on compliance or need insights into security posture, CrowdStrike Falcon Horizon CSPM offers a versatile solution for effective cloud security.
You can get the CrowdStrike Falcon Horizon with a 15-day free trial.
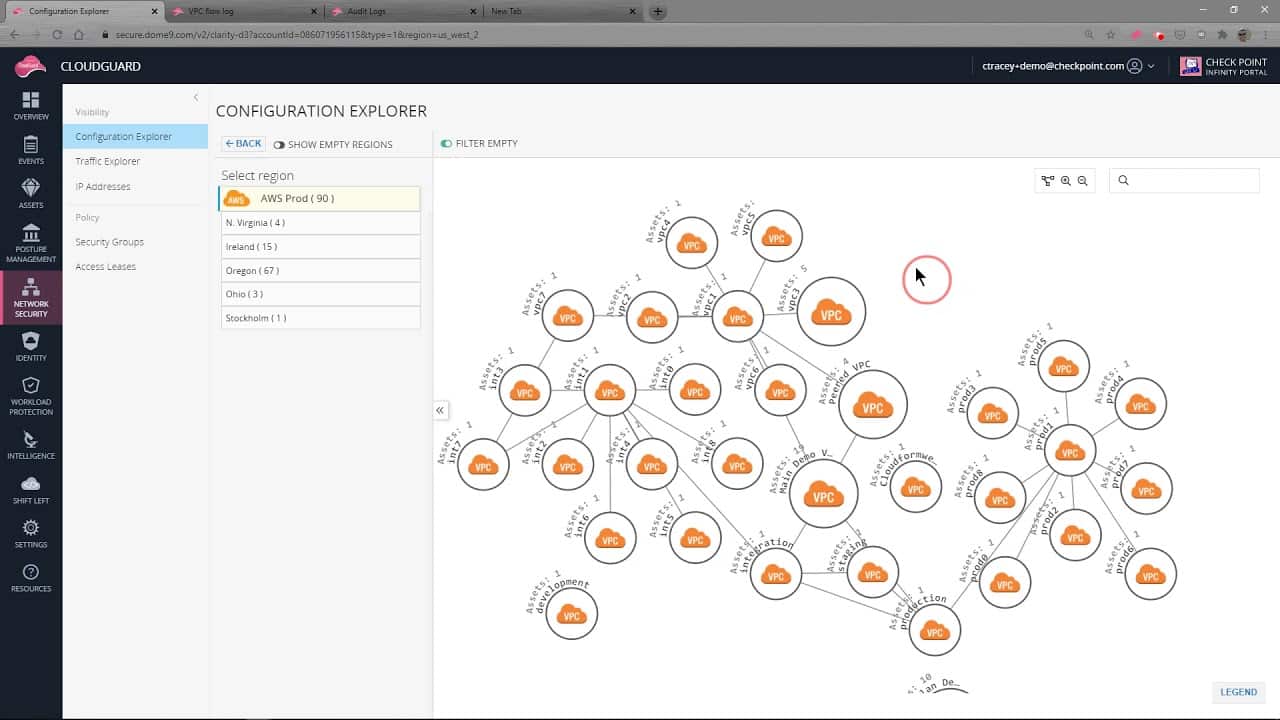
5. CloudGuard Posture Management
CloudGuard Posture Management is a tool designed to aid you with visualizing your cloud security posture and providing helpful automation to simplify compliance and governance in multi-cloud environments.
Key Features:
- Kubernetes monitoring.
- Prioritization and automatic remediation of events.
- In-depth visibility.
- Access control features.
- Detects intrusions and irregularities automatically
- Automated regulation compliance and governance
Why do we recommend it?
Our testing of CloudGuard Posture Management revealed it to be a powerful CSPM tool with excellent visualization features and automated regulation compliance and governance. We assessed its Kubernetes monitoring, prioritization, and automatic remediation capabilities, finding it to be a valuable asset for visualizing cloud security posture.
The tool’s access control features and automated compliance enforcement addressed our need for comprehensive cloud security across multi-cloud environments. What we liked about it was the seamless visualization and enforcement of security best practices, ensuring a robust and compliant infrastructure.
The tool enforces cloud security best practices and policies across all of your projects, accounts, VMs, and virtual networks to ensure your data never falls into the wrong hands.
CloudGuard helps you scale up your operations across a variety of different cloud platforms including Azure, GCP, and AWS. Another excellent feature of CloudGuard is its ability to protect your data against insider threats. With insider threats on the rise lately, one can never be too careful.
The tool allows you to control IAM roles and users, which can help your administrators create granular permission structures across your cloud environment. Automating governance and compliance also lets you pour your administrators’ efforts into less tedious tasks.
The tool also performs regular audits to detect irregularities and provide trustworthy visibility. In case a threat slips by, or a misconfiguration is left standing, the tool allows you to automatically remediate events and prioritize them according to pre-set metrics.
Who is it recommended for?
CloudGuard Posture Management is recommended for businesses looking for visualization features, automated regulation compliance, and governance in multi-cloud environments. Its support for Kubernetes monitoring and access control features makes it suitable for organizations with complex cloud infrastructures. The tool’s automated enforcement of cloud security best practices caters to sectors that prioritize comprehensive security across projects, accounts, VMs, and virtual networks.
Whether you’re dealing with access control or automated governance, CloudGuard Posture Management offers a robust solution for effective cloud security management.
You can request a free demo on the company site.
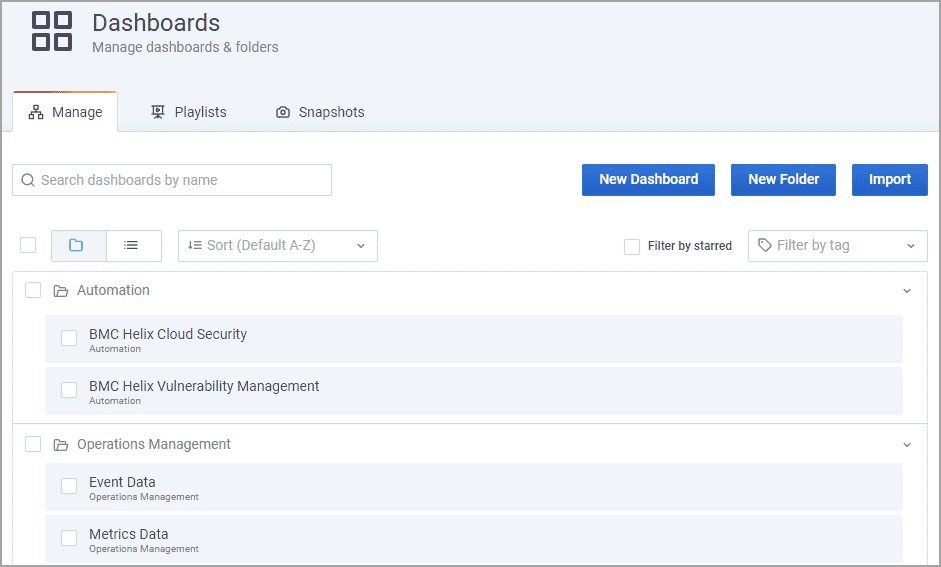
6. BMC Helix Cloud Security
BMC Helix Cloud Security is an easy-to-use CSPM tool made with agile environments in mind. The tool helps you automate config checks and remediation across your IaaS, PaaS, multi-cloud, on-prem, and hybrid cloud environments. One of the best parts of this tool is that the automated remediation feature doesn’t require any coding skills to use.
Key Features:
- Provides you with a cloud security score.
- Automatic remediation facilities.
- CI/CD integration.
- Wide coverage and in-depth visibility.
- Dependency mapping capabilities.
- Excellent reporting features.
Why do we recommend it?
In our comprehensive evaluation, BMC Helix Cloud Security proved to be an indispensable tool with its outstanding dependency mapping features and exceptional reporting capabilities. Throughout our testing, it consistently delivered continuous scanning of our entire infrastructure, providing a comprehensive view of our cloud security posture. The tool’s ability to generate a cloud security score facilitated quick assessments, making it an essential component of our security toolkit.
The BMC Helix Cloud Security provides advanced analytics and tracking capabilities to help you find threats and aid you in improving your business’ efficiency and enhancing its security. It also simplifies patching processes, hastening them and ensuring you’re only installing security patches.
BMC Helix also provides asset discovery and dependency mapping features. These can be incredibly useful when you want to analyze the efficiency of your infrastructure. As an agentless, lightweight tool, it’s very simple to install and easily scales to any business size. The tool easily conducts blind-spot detection and creates audit assessments to keep you up to date with any vulnerabilities or out-of-date software in your infrastructure.
The tool also provides out-of-the-box policies such as GDPR, PCI, and CIS. It also supports using cloud advancement tools to update user data. The MBC Helix will also detect anomalies and ensure the configuration integrity of your containers. Finally, it has standout reporting features, providing highly specialized, in-depth reports at the press of a button.
Who is it recommended for?
BMC Helix Cloud Security is tailored for businesses operating in agile environments, providing a user-friendly experience. Its automated remediation feature, requiring no coding skills, makes it accessible to a wide range of users. The tool’s scalability ensures suitability for different cloud environments, including IaaS, PaaS, multi-cloud, on-premises, and hybrid setups.
Various sectors can benefit from this tool, particularly those prioritizing efficiency, as it simplifies patching processes and ensures the installation of only essential security patches. Businesses aiming for regulatory compliance, such as GDPR, PCI, and CIS, will find the out-of-the-box policies invaluable. Administrators seeking granular control over permissions will appreciate the tool’s asset discovery and dependency mapping features.
You can get a free trial from the company site.
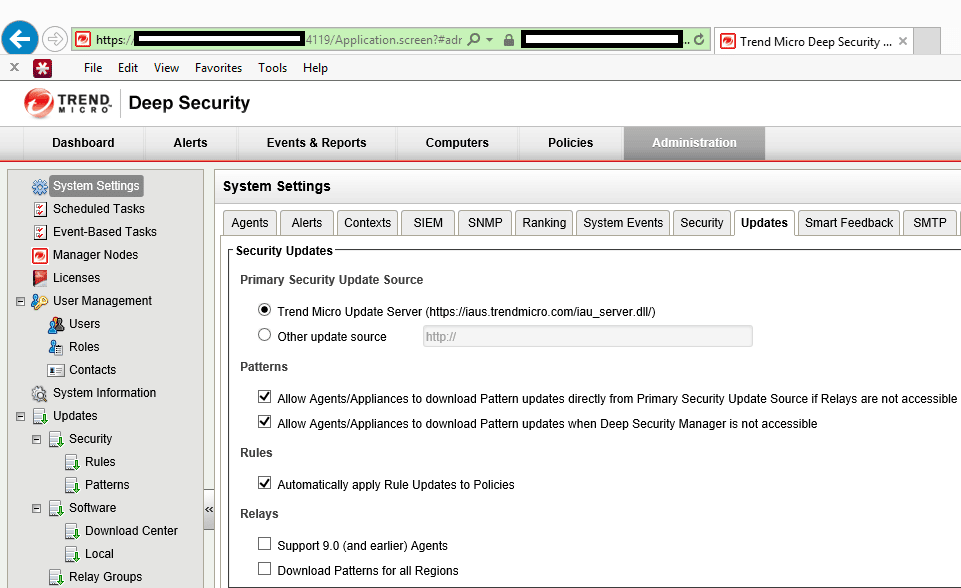
7. Trend Micro Hybrid Cloud Security
Trend Micro Hybrid Security is a holistic solution aiming to provide organizations with everything they need when it comes to cloud security. This flexible solution secures your entire infrastructure while monitoring it constantly for a sign of threats or misconfigurations.
Key Features:
- Automated deployment and discovery features.
- IoC detection.
- Holistic security solution with a single console.
- Real-time monitoring and detection.
- Easily integrates into the CI/CD pipeline.
- Full visibility.
Why do we recommend it?
Trend Micro Hybrid Cloud Security emerged as a top-tier solution during our evaluations, offering a holistic monitoring experience with remarkable automated deployment and discovery features. Throughout our testing, the tool showcased its flexibility by seamlessly integrating into CI/CD pipelines, providing real-time monitoring and detection across diverse cloud infrastructures. Its single-console holistic security solution simplifies the management of cloud security, making it an invaluable asset for our cloud-oriented operations.
The tool can be easily integrated into the CI/CD pipeline and supports the Azure, AWS, and Google cloud toolchains. To provide your business with the utmost efficiency, the tool relies on its automated deployment and discovery capabilities.
Trend Micro helps you monitor your entire infrastructure from a single security management dashboard. This helps your technicians as they won’t have to deal with multitudes of consoles and dashboards to get the full picture of your cloud infrastructure.
The tool facilitates flexible cloud security migration and secures your file storage, servers, and containers. It’ll also perform real-time analysis of your infrastructure. Finally, the Trend Micro Hybrid Cloud Security provides not only automated policy management but also a 24/7 MDR(Managed Detection Response) service.
Who is it recommended for?
Trend Micro Hybrid Cloud Security caters to organizations seeking a flexible and comprehensive cloud security solution. Its automated deployment and integration into CI/CD pipelines make it an excellent choice for businesses looking to streamline security processes. The tool’s support for Azure, AWS, and Google cloud toolchains ensures compatibility with popular cloud environments.
This solution is ideal for businesses aiming for a unified security management approach, as it provides full visibility from a single security management dashboard. Trend Micro’s emphasis on real-time analysis and automated policy management makes it suitable for organizations with a focus on efficiency and continuous security monitoring.
The Trend Micro Hybrid Cloud Security comes with a 30-day free trial.
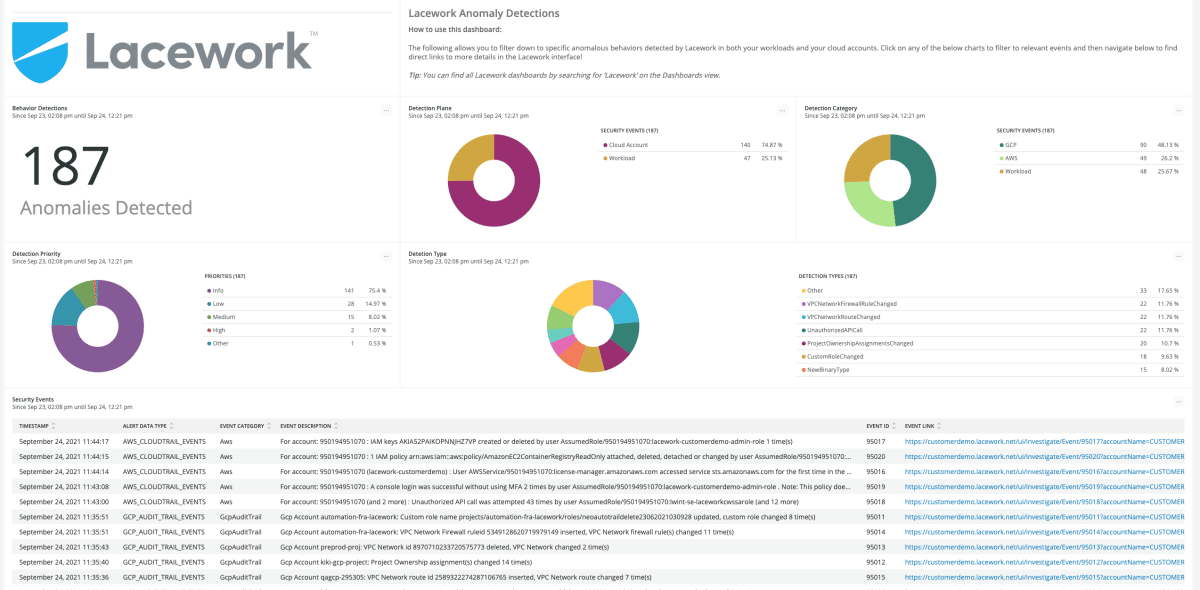
8. Lacework
Lacework is yet another cloud security platform that provides a highly automated and scalable architecture, providing you with complete cloud security and compliance across your GCP, Azure, AWS, and private cloud infrastructure.
Key Features:
- Excellent reporting features.
- Risk prioritization features.
- Machine learning makes a lot of common tasks much smoother.
- Behavioral analysis capabilities.
- Robust alerts system.
Why do we recommend it?
Lacework proved to be an innovative CSPM solution during our rigorous testing, leveraging machine learning to deliver sophisticated features. The tool’s focus on behavioral analysis capabilities set it apart, providing us with a highly automated and scalable architecture. Lacework’s robust alerts system and risk prioritization features, empowered by machine learning, significantly enhanced our ability to detect, monitor, and resolve threats efficiently. It demonstrated a commitment to providing contextual information for configuration and compliance issues, making it a standout choice in our evaluation.
The tool relies on machine learning to provide some of the most innovative features on the market today. It uses ML to help admins detect, monitor, and resolve threats and vulnerabilities more efficiently. Furthermore, Lacework provides you with contextual information that covers any configuration or compliance issues that might’ve arisen.
The tool provides excellent, insightful reports to help facilitate productive inter-team communication. It’ll also help you detect threats, find suspicious activity, and any misconfigurations that might leave room for a malicious actor to get into your infrastructure.
Lacework also provides behavioral analytics and lets your administrators prioritize risks based on their preferences. The tool also aids managers in workflow management and adapts your infrastructure to known cloud security best practices.
Who is it recommended for?
Lacework is an ideal solution for organizations with a focus on advanced security measures and a preference for machine learning-driven features. Its risk prioritization capabilities make it suitable for businesses looking to efficiently manage and address security risks based on their specific criteria. Lacework’s scalability and support for multiple cloud environments (GCP, Azure, AWS, and private cloud) position it as a valuable asset for enterprises with diverse cloud infrastructures.
While Lacework is designed with larger businesses in mind, its machine learning features and risk prioritization can benefit organizations of varying sizes, provided they prioritize advanced security measures. If your business values automated and scalable security architecture with a focus on behavioral analysis, Lacework is a strong recommendation.
You can request a free trial on the company site.
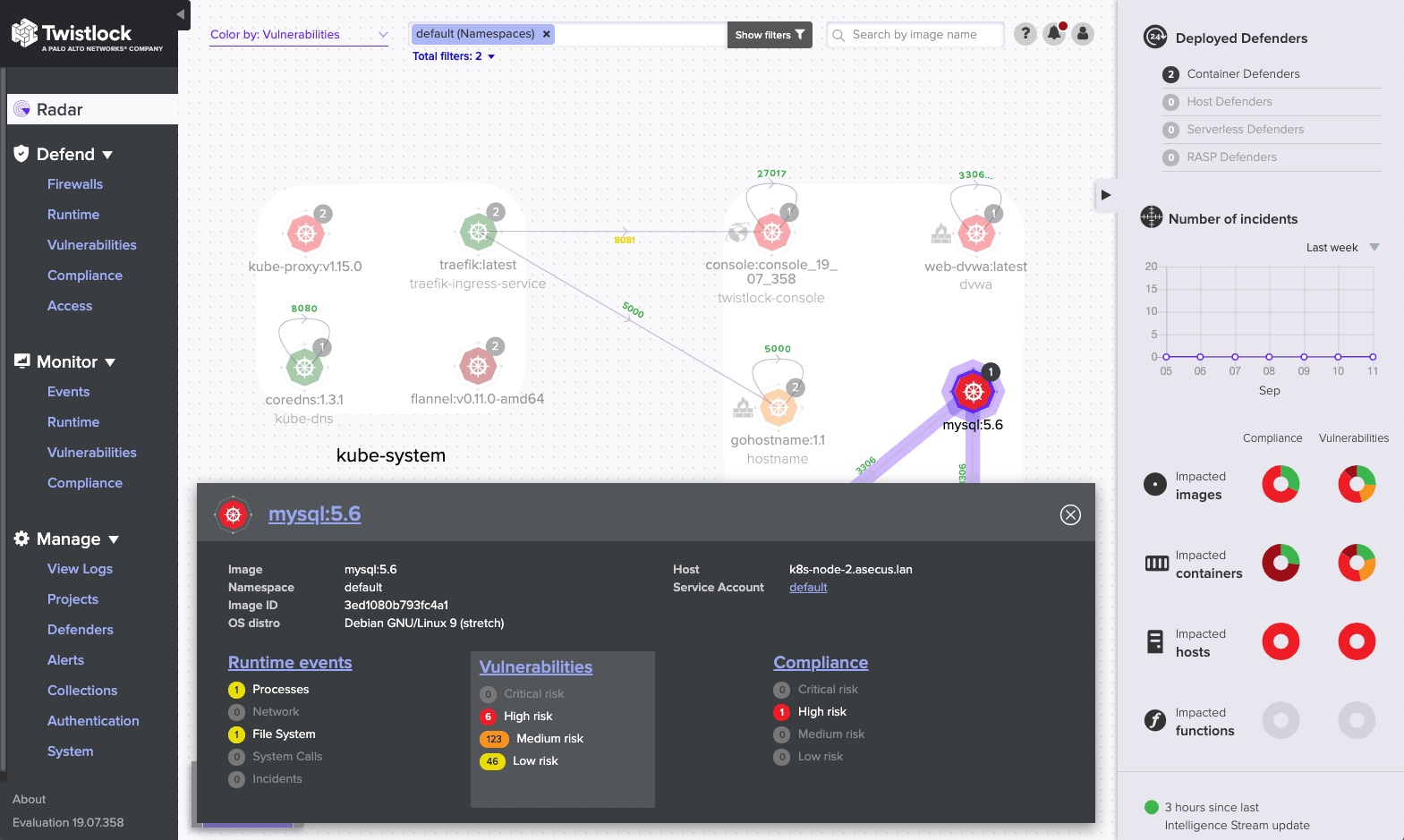
9. Prisma Cloud
Prisma Cloud is a cloud-native CSPM tool providing excellent visibility and a variety of advanced features for keeping track of your cloud security posture. The tool supports container image sandboxing, providing threat discovery through the inspection of all of your files, processes, and pre-deployments.
Key Features:
- API security features.
- Enterprise-focused.
- Blind-spot detection.
- Full-stack runtime protection capabilities.
- IaC template and container image scanning.
- Microsegmentation features.
- Malware scans on your public cloud storage.
Why do we recommend it?
Prisma Cloud stood out as an advanced and enterprise-focused CSPM tool during our comprehensive testing. With full-stack runtime protection capabilities, IaC template scanning, and container image scanning, Prisma Cloud offers a comprehensive suite of features for cloud security. The tool’s emphasis on API security, blind-spot detection, and microsegmentation features adds an extra layer of sophistication to its capabilities. Additionally, Prisma Cloud’s ability to integrate seamlessly with various third-party software makes it a versatile choice for enterprises with diverse technology stacks.
The tool is cram-packed with enterprise-focused advanced features. You can easily eliminate blind spots and the Prisma Cloud will streamline your alerts to reduce fatigue. If you’re looking for a single purchase that will provide you full control over your entire infrastructure within a single agent framework, the Prisma Cloud might be just the tool for you.
Prisma Cloud supports API security and monitoring, as well as full-stack runtime protection and network visibility. It will also regularly back up the important segments of your infrastructure to ensure you can restore them at will.
The tool can also integrate brilliantly with dozens of popular 3rd party software. This, together with its flexibility in dealing with different hybrid or multi-cloud environments makes it a great choice for high-tech enterprises.
The tool will also provide you with IaC (infrastructure-as-code) template scanning and can scan container images automatically or manually. It also provides behavioral monitoring capabilities.
Who is it recommended for?
Prisma Cloud is strongly recommended for enterprises seeking an advanced CSPM tool with a focus on comprehensive cloud security measures. Its support for API security, blind-spot detection, and microsegmentation features make it particularly well-suited for organizations with complex and dynamic cloud environments. The tool’s integration capabilities also make it an excellent choice for enterprises with diverse third-party software requirements.
While Prisma Cloud is an enterprise-focused tool, its flexibility in dealing with different hybrid or multi-cloud environments can benefit businesses of varying sizes. Organizations looking for a single purchase that provides full control over their entire infrastructure within a single agent framework will find Prisma Cloud to be a valuable asset.
You can request a free trial on the company site.
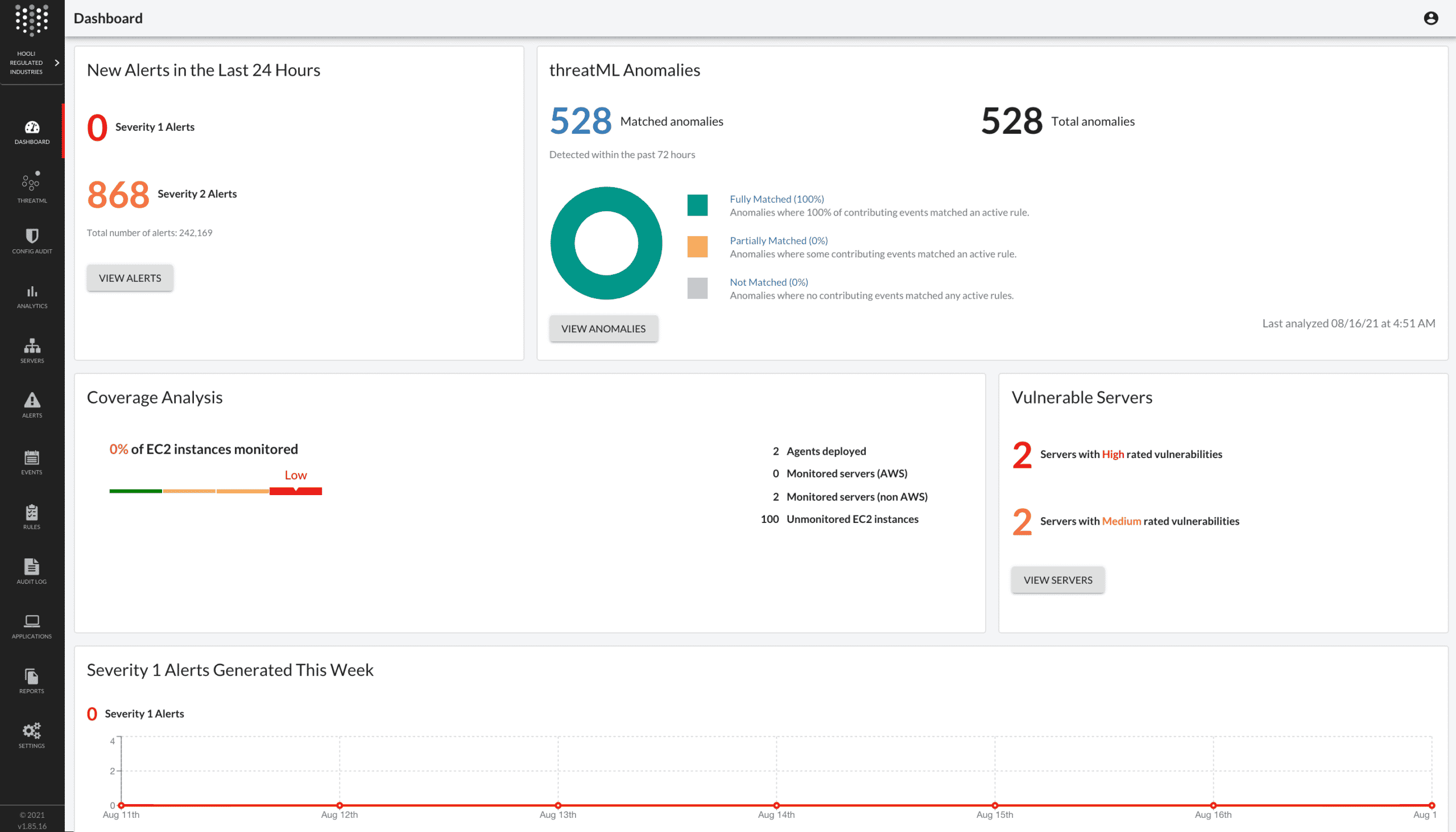
10. Threat Stack
Threat Stack is a modern CSPM tool made with modern app infrastructures and cloud-native environments. It aims to provide complete visibility across all of your cloud management consoles, apps, containers, etc.
Key Features:
- Machine learning allows for increased sophistication.
- Quite customizable.
- Anomaly detection capabilities.
- Secures Kubernetes and containers.
- CloudTrail monitoring capabilities.
Why do we recommend it?
Threat Stack, a modern CSPM tool designed for modern app infrastructures and cloud-native environments, impressed us with its advanced features and customizable nature. Leveraging machine learning for increased sophistication, Threat Stack offers anomaly detection capabilities, secures Kubernetes and containers, and provides CloudTrail monitoring capabilities. Threat Stack effectively addressed our need for complete visibility across all cloud management consoles, apps, and containers. With machine learning capabilities, it provided in-depth insights into threats and vulnerabilities, allowing us to respond swiftly.
The tool has a variety of advanced features including policy and incident management, configuration audits, vulnerability assessments, and more. This is another tool that takes advantage of machine learning to exceed its predecessors in sophistication.
Threat Stack attempts to combine rigid rules, full-stack telemetry, and machine learning to provide the best CSPM experience. The tool also supports CloudTrail monitoring and IAM policy management. When it comes to threat response and detection, there are few tools as good as Threat Stack.
Threat Stack provides excellent application infrastructure protection features, in addition to conducting EC2 inventory. The tool is also quite customizable, letting you configure its rules and alerts in great detail. It also aids your business in ensuring that you’re compliant with data regulation policies.
Who is it recommended for?
Threat Stack is recommended for organizations with modern app infrastructures and cloud-native environments seeking a CSPM tool with advanced features and customization options. Its support for anomaly detection, CloudTrail monitoring, and Kubernetes security makes it suitable for businesses with diverse cloud environments. The tool’s focus on policy management and vulnerability assessments positions it as a valuable asset for organizations prioritizing comprehensive cloud security.
While Threat Stack is quite customizable, for beginners, the tool’s UI will be a bit challenging to navigate. Therefore, organizations considering Threat Stack should ensure that their team is comfortable with the tool’s interface or take advantage of a live demo available on the company site.
You can request a live demo at the company site.