Windows event logs record every action taken on a Windows machine. Every click and interaction is recorded in these logs, making them a crucial troubleshooting asset. Because of this, learning event log management can help you resolve issues.
Unfortunately, once your server setup goes over a couple of servers, managing separate event logs become practically impossible. To solve this issue, Windows has a tool called WEF (Windows Event Forwarding).
Event log forwarding enables system admins to centralize client and server event logs in a Windows-based ecosystem. This allows them to monitor events without being connected to individual servers. The standard for log forwarding is the DMTF WS-Eventing standard, it is part of the WS-Man (Web Services-Management) protocol, which is part of the framework built into all Windows Servers.
Log messages are steadily growing in importance, despite being almost ignored for decades. Today, admins around the world are scurrying to save and analyze log messages from their system. However, this can be difficult.
Today, we’ll lead you through log forwarding one step at a time.
Event Log Message Standards
There are two main standards used by log messages:
- Syslog – An extremely common open standard used on Linux systems. Some devs for 3rd party software decide to use this standard.
- Windows Events – A standard that adheres to proprietary Microsoft standards shared across their products. Most third-party products will use this standard.
Event log forwarding is simply the process of consolidating these two kinds of logs into one cohesive whole that’s easier to manage and search.
WMF Framework
Today, we’ll walk through setting up Event Log Forwarding in Windows Server 2012 R2, as well as configuring a source server and collector servers. You can use Windows Server 2008, Vista, or later as an event collector.
Event Log forwarding is convenient because you don’t need to install a collection agent on your collectors; it’s built-in for Windows Server servers. Event log forwarding is excellent for larger networks as collectors can forward to each other to ensure maximum speed. You can also use the HTTPS protocol to ensure message security.
Collectors and Receivers
To gather all of your log messages in one place, you need to create a bridge between the two log message standards. This is easiest to do by using a 3rd party tool as a Windows log message manager will only collect Windows Event logs, while completely ignoring Syslog messages. On the other hand, a Linux log manager would collect Syslog messages, but wouldn’t deal with Windows Event messages.
This means that in an infrastructure where both Linux and Windows systems are present, admins must maintain a minimum of two log message stores, each of which would only hold either Syslog or Windows Event logs. With that being said, this is inefficient and opens your systems up to intrusion.
To solve this issue, we need to find a way to take Windows Event messages and turn them into Syslog messages, or vice-versa. Doing either of these would allow us to store all logs in one location, and could be searched through more easily, all the while making you more resistant to attacks. Alternatively, we could take both Windows Events and Syslog messages, and transfer them to a third format.
Event Log Forwarders & Log Servers
For event log forwarding to function, the event log forwarder will have to be an on-premises system. However, neither the log server nor the consolidator has to be on-prem. Because of this, you can take your pick between on-site and hosted log servers.
SaaS Models
A lot of hosted systems will include a log collector, aka. An Event log forwarder. If this is the case in your ecosystem, you must have the log collector installed on a Windows host on-prem. You’ll usually see this referred to as an agent. Furthermore, if you’ve got a Linux machine, you’ll need to have a Syslog forwarder on one of them to combine your Windows and Linux logs. Many SaaS log file management tools also offer Linux-based agents to make this easier. In case your log file server is on-prem, then the log forwarder and server will stay as separate packages, as the log server is made to be able to handle both Syslog and Windows Event logs.
What Do I Need To Start?
All Event Log collectors can be configured in a variety of different ways. Event log collectors are configured in a way that they can pull logs from any source device. You don’t need to have the source devices configured in any particular way, outside of:
- Ensuring WinRM (Windows Remote Management) is enabled
- WinRM Windows Firewall exceptions are allowed
- The log collector must have read permissions enabled for the logs you want it to collect
Now, there are enough different configurations out there that we could spend the whole article talking about them. For example, setting up user accounts to authenticate that the source of the logs is the source device. However, we’ll simply be going over this standard configuration, in case your computers are set up in a workgroup instead of a domain, it’ll take a bit more configuring to get going.
For this guide, we will only be using the following package:
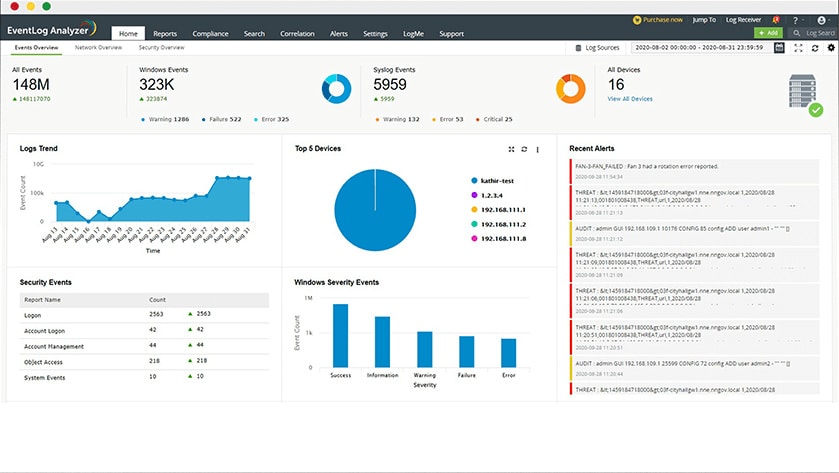
ManageEngine EventLog Analyzer – this is available for a 30-day free trial and it can be installed on Windows Server or Linux.
Event Log Forwarding- Step By Step
ManageEngine EventLog Analyzer is a powerful tool for centralizing event log management and monitoring. Forwarding event logs from devices or servers to EventLog Analyzer ensures that logs are aggregated, analyzed, and stored for auditing, compliance, and troubleshooting. This step-by-step guide will walk you through setting up event log forwarding to the tool.
Step 1: Install and Set Up ManageEngine EventLog Analyzer
- Download and Install: Obtain the installer for EventLog Analyzer from the ManageEngine website and follow the installation wizard to set it up.
- Access the Web Console: Launch the application and open the web-based interface using the default URL provided during installation.
- Configure Basic Settings: Set up user preferences, storage settings, and any required compliance parameters to suit your environment.
Step 2: Configure Event Sources
- Add Log Sources: In the EventLog Analyzer interface, go to Settings > Manage Devices > Add Device.
- Select Device Type: Choose the type of source you want to monitor, such as Windows servers, Linux/Unix systems, or network devices.
- Provide Device Details: Enter the hostname or IP address of the device and any required credentials for authentication.
Step 3: Enable Event Log Forwarding
For Windows Devices:
- Open Windows Event Viewer: On the target device, launch the Event Viewer application.
- Configure Subscriptions: In the Subscriptions section, create a new subscription and specify the events you want to forward.
- Set Forwarding Destination: Point the forwarded events to the IP address and port of the EventLog Analyzer server.
For Syslog Devices:
- Enable Syslog Forwarding: Configure syslog forwarding in your device settings.
- Specify EventLog Analyzer as Destination: Enter the server’s IP address and the appropriate UDP/TCP port (default is 514).
Step 4: Verify and Monitor
- Check Incoming Logs: Navigate to the Dashboard in EventLog Analyzer to verify that logs are being received from the configured devices.
- Set Up Alerts: Create custom alert rules to monitor specific events or anomalies.
- Generate Reports: Use built-in reporting features to analyze log data for compliance or troubleshooting.
By following these steps, you can efficiently forward logs to ManageEngine EventLog Analyzer, ensuring centralized monitoring and streamlined log management.
WEC Server Limits
WEC servers have limited scalability. For most commodity machines, you’ll find a stable WEC server that can deal with around 3,000 events per second. Three factors affect the scalability of WEC servers:
- Disc Write Speed WEC does not immediately process or validate logs. It buffers and logs received events to the local event log file. Local event log files can only be written at a rate under the disc write speed. You can alleviate this concern if you isolate the local event log files to their arrays, or by using discs with a higher write speed.
- TCP Port Count Although WEF sources don’t need a persistent connection with the WEC server, their disconnect after they’ve sent their events is not instant. Because of this, only a limited number of WEF sources can be connected to your WEC server. This is dictated by the count of TCP ports on it.
- Registry Size To store, bookmark, or source heartbeat data, a registry key corresponding to the FQDN(fully qualified domain name) of a WEF client is generated for each device connected to a WEF subscription. When these aren’t purged of inactive clients, the number of registry keys can quickly grow overwhelming.
By monitoring event logs, you’ll be able to get a better grasp of your system metrics, find process bottlenecks, and improve your ability to find security vulnerabilities. In case you keep your log data, you should either conduct batch processing or have a way to look at event logs in real time. Event logs can be monitored either manually or automatically, with most businesses using a tool to make it easier.
Is Manual Log Monitoring Scalable?
Most small businesses start out monitoring their logs manually by having technicians look over them routinely. While this can work in a small business, as your network grows in size, the number of logs that need to be monitored grows exponentially. This is why in medium to large businesses, manual log monitoring is practically unfeasible.
Because of this, most businesses use log monitoring solutions to help centralize event monitoring in one place. These tools allow you to customize the way your logs are parsed and processed, as well as set up triggers and responses based on your own rules. A large benefit of this is that it increases security as if a machine is breached they’ll be unable to gain access to your logs, and you’ll be able to more easily track the perpetrator down.
The Benefits of Event Log Monitoring
It Improves System Performance
Event log monitoring tools archive your previous logs, which lets you conduct data analysis by looking at all of them. This can help you extrapolate which processes are spending too many resources, causing bottlenecks, or slowing down performance.
If your solution supports real-time monitoring, you can also find smaller, cascading issues by monitoring your logs in real time. Customizable tools will oftentimes let you pick which logs you want to be looking at, and which ones it can filter out. This lets you get the most out of your event log management experience.
Increasing Efficiency
Manual event log monitoring is common in smaller businesses, however, they too benefit from getting a solution to conduct event log monitoring for them. Doing it manually means someone is constantly looking at the logs, which means either more people working in shifts around the clock or leaving your infrastructure unmonitored during some hours. If a critical issue were to arise during these hours, you wouldn’t be able to react in time and could face hours-long delays before your services are back up. This leads to dissatisfaction in your end-users, which is something that should be avoided as much as possible.
Using log event monitoring software lets you dodge this issue and minimizes the time it takes for you to detect and resolve issues. Since event logs grow exponentially with the size of your infrastructure, it’s in your best interest to streamline and automate the process as much as possible.
Automate Problem Repair
Another large upside of automated log monitoring software is that you can set it up so that it takes an action whenever a specific event happens. Oftentimes, runtime problems can be solved with easy fixes that can be scripted. This lets you reduce the time you spend troubleshooting and fixing simple issues, it also helps your uptime without requiring human intervention.
Enhance Cybersecurity
Regardless of a business’s size, IT security should always be at the forefront of its strategy. If a malicious actor gains access to your data, especially data protected by laws, your business could end up losing massive amounts of revenue.
Log monitoring can often let you detect these issues before they cascade into security disasters. By securely keeping logs and letting an automated solution constantly keep tabs on them, you’re saving a lot of money in potential fines.
Helping You Comply With Regulations
Regulatory compliance doesn’t apply to private entities in most cases. However, if your firm is, or is looking to go public, you’ll need to comply with regulatory standards. Tools often incorporate assistance with complying with regulations in their features. This means your business will have an easier time complying with them and will avoid getting fined for mistakes.
Closing Words
Whether or not you’re looking to implement event monitoring, event log forwarding is a great asset to have in any business. Event log forwarding allows you to gather logs in one, easily accessible place. From there, you can monitor them automatically or manually, with automated software being favored by larger businesses.