Are you familiar with the term virtual patching? Known vulnerabilities are the largest source of cyberattacks these days. 99% of all successful cyberattacks are performed using vulnerabilities in the system that are already known to higher-level executives within the company. This means that one of the biggest security risks today is not the vulnerabilities you haven’t found, but the ones you haven’t addressed.
These flaws often go without patching for a while, generally, it takes 69 days for a company to patch known vulnerabilities in the system. The attacks targeting these issues are usually quite hard to defend from, leading to many companies looking to patch the solution. This is essentially just a type of code rewriting sections of your system to alleviate common attack vectors.
Patching places its focus on helping with issues that affect the functionality of code within your system. Today, this is more focused on the increasingly sophisticated techniques attackers use, because of this, patching is becoming more and more important in the business world.
For a corporation, reputation is everything. If your customers and partners don’t trust you, your operations and growth will be heavily hindered. Because of this, it’s in every enterprise’s interest to address their vulnerabilities as quickly as possible. This is where virtual patching excels.
Virtual patching automatically accounts for the flaws found within your system to shield them from being used as an attack vector and only fix the issue later. Much like software updates(or patches), virtual patching will shield you against certain attack vectors. The biggest difference is that virtual patching isn’t deployed on a single machine but on an entire network.
Virtual patching falls into the proximity control category because it stops threats before they can accomplish their goals.
Virtual patching is, essentially, a security tool you can use in an emergency in order to be able to immediately fix vulnerabilities during an attack.
But when should you employ virtual patching? What does it even do? Read on to find out!
It serves as an emergency security tool that organizations can use to instantly address vulnerabilities on affected endpoints and servers.
Why You Need Virtual Patching
The most challenging task for many security teams is figuring out how to keep assets safe from current and future threats. Malware tends to take advantage of vulnerabilities that are already known to the company itself. These vulnerabilities are known as CVEs; when a vulnerability is a CVE that means that the company is aware of the issue, maybe even how to fix it, but they haven’t gotten around to it yet.
According to Edgescan statistics, 67.7% of all businesses’ assets have at least one CVE, impacting their future functioning.
The easiest solution to present is to patch the affected system against the CVEs found to prevent attackers from using it as a vector. Whether we’re talking about a front-end or back-end system, it’s crucial to fix any vulnerabilities found on it.
Even vulnerabilities that have been deemed not critical can be an attack vector for malicious agents. Often, attackers will use more minor vulnerabilities to get “leverage” in the system and have an easier time accessing more lucrative attack vectors.
Finding vulnerabilities on time and controlling incoming traffic is essential in enhancing your businesses’ resistance to malware.
How Are Patching Problems Solved With Virtual Patching?
Virtual patching can be both a solution for coding flaws and cause frustration for system administrators. So, why is patching out vulnerabilities quickly and accurately so crucial for a business?
Patching a vulnerability “properly” can take quite a while, ranging from a few days to entire months. This is especially true when the vulnerability affects the core functioning of the application in question.
Sometimes, patching might take even longer than expected due to a variety of factors:
- Costs: Software upgrades can cost a penny, and sometimes vulnerabilities are caused by older systems or hardware. Occasionally, patching will require a complete rebuilding of an older application. It might simply get delayed because these things can cost quite a bit.
- Official Patch Delay: Sometimes, the vendor does not provide patches on time; in these cases, patches are often delayed.
- Preserving Uptime: Preserving the uptime of specific servers and networks can be critical to a business, which can delay patching opportunities.
These cases make virtual patching a very attractive alternative as a cost-effective, short-term solution.
Cyber attackers are always looking for new ways to exploit vulnerabilities and are always searching for unknown attack vectors to use. Research done by FireEye shows that most attacks happen when a vulnerability hasn’t had an official patch issued yet, or a few days after it did.
What Issues Does Virtual Patching Prevent
The speed at which attackers operate to exploit the vulnerabilities within your system show how necessary it is to provide patches quickly and efficiently. With that being said, not all vendors will provide patches on time, and there might be delays within the enterprise slowing the process. When virtual patching isn’t used to stop this, you might face some of the following issues:
- Security measures compromises that leave you open and vulnerable to other attacks.
- Data leaks that air your business data and secrets for everyone to see.
- Reputation losses as your customers trust your business less for succumbing to an attack.
- Financial losses when it comes to recovering stolen assets or fixing damage caused.
- Long-term damage to your systems.
With more and more vulnerabilities appearing year in and year out, it becomes tough for businesses to patch issues with the appropriate speed with their limited resources. Because of this, technologies like virtual patching can help alleviate the pressure known vulnerabilities place upon your business by protecting both known and unknown vulnerabilities.
Patching Vulnerabilities Using Virtual Patching
Virtual patching, also referred to as Web Application Firewall (WAF) is the implementation of a layer of security policy to stop attackers from exploiting vulnerabilities in your system. An excellent virtual patching solution will be able to look at malicious activity coming from traffic and find and stop intrusions. Quality solutions will also adapt to cloud deployments, physical environments and stop attacks targeting web apps.
Security administrators can review, test, and schedule the traditional patches using virtual patching to minimize the risk of leaving the system down or open to attacks.
Traditional patching methods interfere with libraries, OSs, or the computers that they’re on. Virtual patching does none of this. Instead, it focuses on fixing the issue at hand by interfering with the malicious behavior directly. Virtual patching targets traffic using known vulnerabilities in the system and will immediately take steps to interrupt and block the traffic before there’s time to exploit any of the system’s weaknesses.
Virtual patching lets you protect your applications and enterprise without needing to patch them or turn them off. The most significant advantages of virtual patching are that it’s much quicker and doesn’t require app language programming. You can also do it while your servers are up, letting you patch up critical vulnerabilities without impacting performance.
When Is Virtual Patching Important?
- When you need a short-term stop-gap for a critical vulnerability before a permanent patch can be easily installed.
- Before you deploy a permanent patch- permanent patches can sometimes cause new issues, and checking whether they will do this incurs even more delays. Virtual patching lets you get around this initial phase while still keeping up security.
- When an asset or application needs a lot of downtime during patching, something like a pipeline monitoring system will take a while to patch and generally shouldn’t be turned off during the patch. In these scenarios, it’s a great idea to use virtual patching to minimize the risks during downtime.
- In a high-risk situation when attackers have already found a known vulnerability. Using virtual patching can help cut the attack short.
What Are The Benefits Of Virtual Patching?
- Virtual Patching can buy you time to fix known issues – Giving your team time to analyze and correct flaws in the code can be crucial in your cybersecurity approach. In addition, getting time to implement and test patches can be the difference between a successful and failed defense.
- Improves Security – Virtual patching can provide instant security for those sections of your infrastructure that you cannot patch immediately.
- Help With Regulations – Your business will have an easier time fulfilling the requirements put out by the General Data Protection Regulation, PCI, or other regulatory authority
- Flexibility – Virtual patching gives you much-needed flexibility on when and how you roll out updates. You can simply update the security policy without needing to change the code itself directly.
- Speed – You can address issues much quicker with virtual patching than most traditional patching methods. This is a sizable advantage since hacks tend to occur either before or just after a patch is released.
- Cost – Virtual patching solutions tend to be very cost-effective to the company employing them. This is because they’re pretty simple to implement and can help alleviate the need for downtime.
Using Virtual Patching Tools
Virtual patching can be done by using various tools such as application layer filters, WAFs, or Intrusion Prevention systems, as well as simple web server plugins. With that being said, not all of these tools are equivalent in value.
When picking which virtual patching tool you’re going to use, you should be looking for the following:
- The ability to split up HTTP requests into their core components and the ability to analyze these separately and in great detail
- As many anti-evasion capabilities as possible, data sanitization and character encoding are a must, but others are also welcome
- Many tools out there are exclusively signature-based. Instead of this, you should be looking for tools that are capable of implementing complex security rules.
Web Application Firewall or WAF offers a lot of this, which is why the term is often conflated with virtual patching itself. Using a WAF like AppTrana will help out a lot when securing your apps and websites against threats known and unknown. It makes sure you get a highly scalable and easy-to-use deployment that can protect you against the most common threats.
SolarWinds Patch Manager – FREE TRIAL
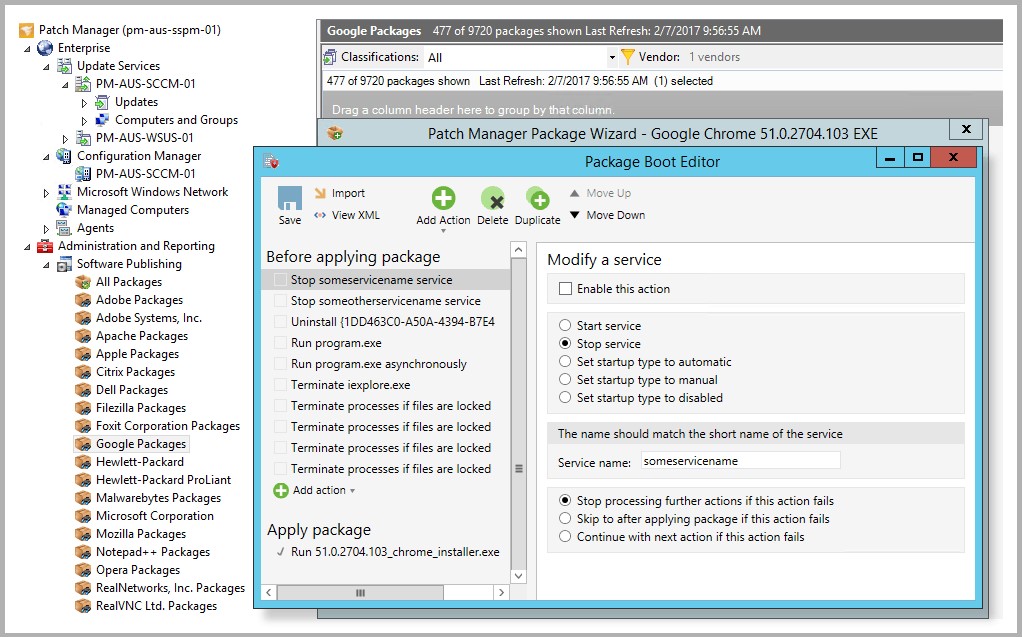
In our experience, the tool that performed the best is the SolarWinds Patch Manager.
Not only does the tool provide all of the above, but it also serves as a very robust patch manager for more traditional patching methods. It will centralize all of your patching processes and allow you to patch devices even when they’re turned off.
Why do we recommend it
SolarWinds Patch Manager truly came to the rescue when we were grappling with delays and intricacies in our patching process, especially given the complexities of our infrastructure. This tool’s ability to navigate through these challenges with finesse not only streamlined our operations but also highlighted its reliability for tech pros dealing with intricate patching scenarios.
Furthermore, urgent issues can be quickly addressed through the tool’s intuitive dashboard. You can even build custom deployment packages to handle specific kinds of threats. Finally, the tool will automate the virtual patching process to ensure that you get the most out of your endpoint security experience.
Who is it recommended for:
SolarWinds Patch Manager is highly recommended for IT professionals, security teams, and businesses across various industries. Its user-friendly interface and versatile features make it suitable for organizations of all sizes, from small enterprises to large corporations.
Specifically, it caters to IT enterprises dealing with complex infrastructures requiring a streamlined approach to patch management, healthcare organizations aiming to protect critical assets and sensitive patient data, and the finance industry where quick responses to urgent issues are imperative. The tool’s free trial option allows users to explore its capabilities and suitability for their specific needs. You could try out SolarWinds Patch Manager which comes with a fully functional 30-day free trial.
Download the 30-day FREE Trial
https://www.solarwinds.com/patch-manager
Conclusion
With enterprises’ infrastructures ever-growing in complexity, ranging from eminent decentralization to the widespread nature of IoT, cloud, and mobile technologies, more and more vulnerabilities are staying unpatched. As a result, traditional patch management has grown from taking an IT specialist an afternoon to something that can take a whole team weeks.
Because of this, virtual patching has become one of the essential tools in an enterprise’s cybersecurity arsenal. To get the most out of virtual patching, you’ll want to keep in mind public vulnerability disclosures and review your source code and apps for vulnerabilities regularly.
Naturally, virtual patching is also great when it comes to defending from an imminent cyber attack. However, with that being said, virtual patching does not replace traditional, permanent patches.
All virtual patching does is ensure that your apps and devices are protected in the short term. However, often this is all it takes.
Do you use virtual patching?
Did we miss your favorite virtual patching tool?
Let us know in the comments below!