Auditing network security is a crucial element of any modern company. Auditing the IT assets and policies within your network can help you realize its weaknesses.
Furthermore, auditing gives a birds-eye view of your network that can be beneficial when you’re attempting to resolve a specific issue. Performing audits gives you a grasp of how well your enterprise is defended against common threats.
Here’s our list of the best network security auditing tools:
- ManageEngine Log360 – EDITOR’S CHOICE A SIEM service that includes Active Directory auditing and activity logging for compliance auditing in addition to its live activity alerting. Runs on Windows Server.
- ManageEngine ADAudit Plus – FREE TRIAL This package implements user behavior analysis, file integrity monitoring, Active Directory protection, and compliance auditing. Available for Windows Server, AWS, and Azure.
- Site24x7 Network Configuration Manager – FREE TRIAL A hosted configuration management tool that protects network device settings and sits inside a broader monitoring and management platform. Get a 30-day free trial.
- Intruder A cloud-based tool paid with a subscription model excellent for a buy it and leave it model of security auditing.
- SolarWinds Network Configuration Manager Made by the reputable SolarWinds company, it combines an extensive list of features with a slick and intuitive GUI.
- Netwrix Auditor One of the best tools if you’re looking for a tool with excellent automation capabilities and a Rest API.
- Nessus A great template-based tool for beginners and advanced users alike.
- Nmap Nmap is an open-source tool with a lot of depth, offering customization if you want it, but still being quite good for beginner users.
- OpenVAS An open-source tool constantly updating its list of over 50,000 vulnerabilities.
Today, we’ll be taking a look at the cream of the crop in network security auditing assets such as vulnerability and port scanners, patch managers, and a variety of other tools that can help your network security.
The Best Network Security Auditing Tools
1. ManageEngine Log360 – FREE TRIAL
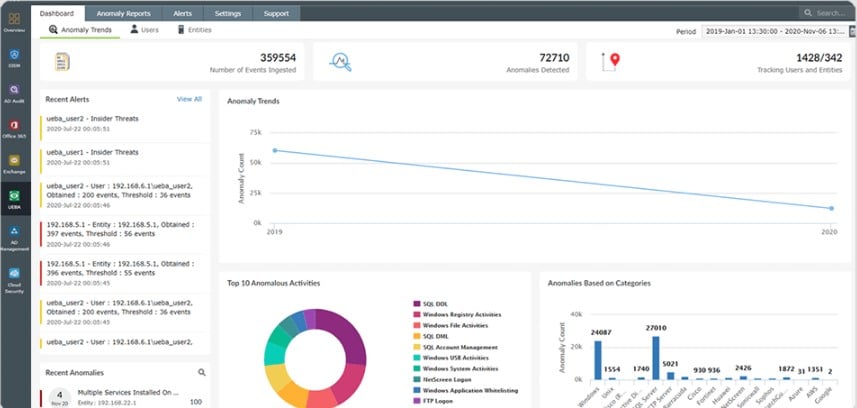
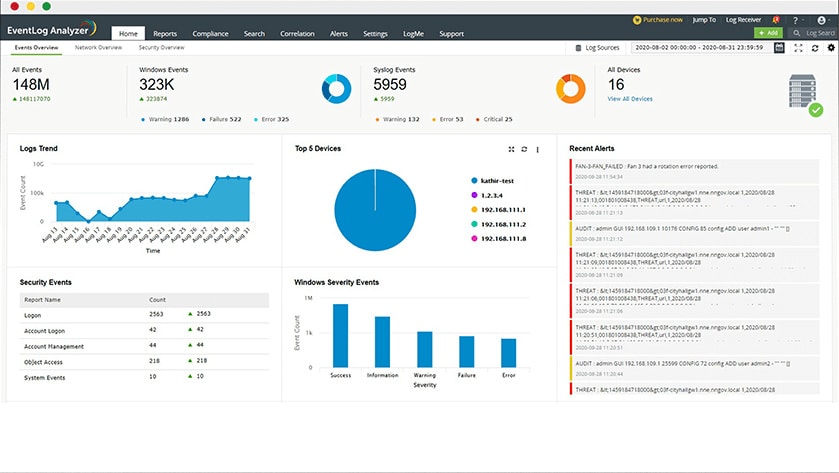
ManageEngine Log360 is a collection of security tools that is headlined by a SIEM service but also includes extensive activity logging and system auditing features. The entire package is able to operate on logs sourced from more than 700 applications and operating systems, which report in different log message formats.
Why do we recommend it?
ManageEngine Log360 emerged as a powerful SIEM service in our extensive trials. Its ability to collect and consolidate log messages from a wide range of sources was instrumental in detecting and addressing security threats promptly. ADAudit Plus, a part of the package, was a gem for monitoring user behavior and Active Directory changes. It efficiently alerted us to suspicious activities, efficiently solving the problem of maintaining compliance and improving network security.
The six tools included in the Log360 package include the EventLog Analyzer, which collects log messages, consolidated their different formats into a common format, stores them, and makes them available for analysis. Logs can be collected from cloud platforms as well as network endpoints.
The Log360 log management system files and archives log messages. This availability of logs stored in an orderly manner is an important requirement for compliance auditing. The package also includes a compliance reporting tool for HIPAA, PCI DSS, FISMA, SOX, GDPR, and GLBA.
Another system included in the Log360 bundle is ADAudit Plus, which assesses the objects and structures in Active Directory, highlighting weaknesses that need to be tightened. The tool logs all activity on the system, attributing the user account involved. This is a good assistant for identifying insider threats or account takeover events.
The SIEM provides live searches through arriving log messages and raises alerts when it discovers suspicious activities. Alerts can be channeled through service desk systems, including ManageEngine ServiceDesk Plus, Jira, and Kayoko.
Who is it recommended for?
ManageEngine Log360 is an excellent choice for businesses seeking robust security tools across various sectors. Its interface caters to both beginners and advanced users. ManageEngine Log360 offers customization options, allowing businesses to tailor the security tools to meet sector-specific needs. It runs on Windows Server and you can access the system with a 30-day free trial.
EDITOR'S CHOICE
ManageEngine Log360 is our top pick for a network security auditing tool because because it combines security information and event management with advanced log management in one platform. It collects and analyzes logs from network devices, servers, applications, and security appliances, giving teams broader visibility into suspicious activity, compliance gaps, and operational risk. The service supports more than 700 log sources, including routers, firewalls, and intrusion detection systems. Real-time alerts, detailed dashboards, and incident management workflows help teams investigate and respond more quickly when predefined security thresholds are crossed. Log360 also strengthens compliance work through reporting for standards such as GDPR, HIPAA, and PCI-DSS. That combination of log analysis, alerting, and compliance support makes it a strong fit for organizations that need more than basic auditing.
Download: Get a 30-day FREE Trial
Official Site: https://www.manageengine.com/log-management/download.html
OS: Windows Server or Cloud
2. ManageEngine ADAudit Plus – FREE TRIAL
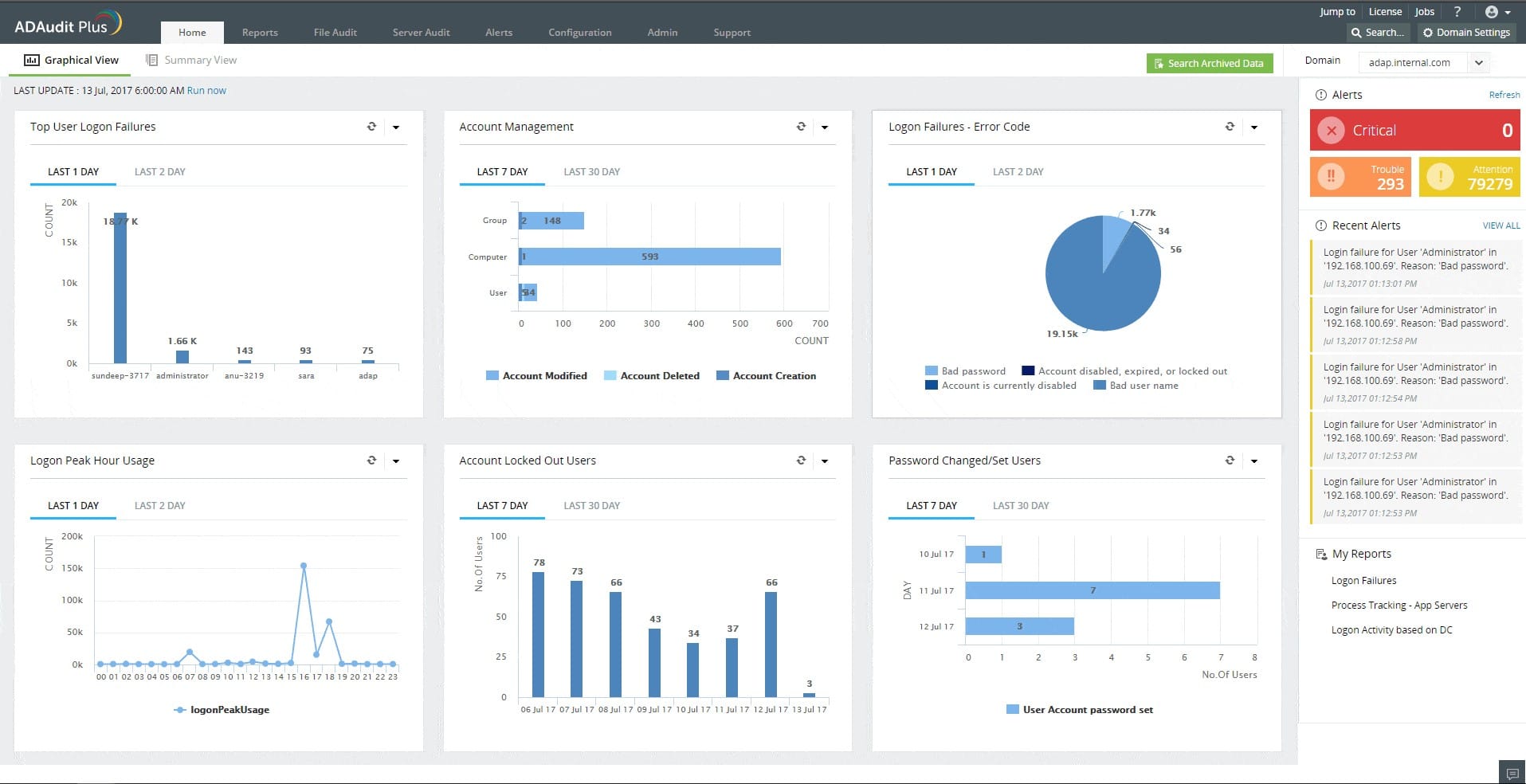
ManageEngine ADAudit Plus is designed to audit file access activity and compile user behavior analysis. The logs that this tool creates are funneled through to a security auditing process.
Why do we recommend it?
Our experience with ManageEngine ADAudit Plus was marked by improved file access monitoring and user behavior analysis. It helped us create a more secure environment by efficiently auditing and reporting on file access activities. ADAudit Plus not only strengthened our security but also ensured compliance with industry standards. Its Active Directory protection and alerting capabilities were invaluable in identifying and responding to threats.
There are three editions for this package and the lowest of these offers workstation activity monitoring and recording plus compliance auditing and reporting. The next edition up extends its monitoring and auditing services to servers.
The top plan provides activity logging and compliance auditing and also implements Active Directory protection. This service raises an alert if an objection AD is changed. Alerts appear in the system console but you can also set them up to be forwarded as notifications by email or SMS.
The auditing service in the tool is implemented by templates, which are a combination of search strings and layout formats. By running one of these reports you get a summary of the stored logs that record file access activity.
These audit reports also count as compliance reporting facilities. The auditing and reporting service can be tailored by specifying which data protection standard you need to follow. Options cater to SOX, HIPAA, PCI-DSS, FISMA, and GLBA.
Who is it recommended for?
ManageEngine ADAudit Plus is recommended for businesses that require in-depth auditing and monitoring of file access activities. ADAudit Plus caters to businesses of all sizes, providing essential tools to fortify security and compliance.
For example, ADAudit Plus caters to healthcare organizations by providing in-depth auditing of file access activities, ensuring compliance with HIPAA regulations, and offering a user-friendly interface for both novice and experienced users in the healthcare sector.
ManageEngine ADAudit Plus is available for installation on Windows Server and you can also get it as a service on AWS or Azure. The workstation logging system forms the heart of the lowest edition, which is free to use. Two paid editions offer logging and auditing for servers (Standard) and logging for workstations and servers plus alerts on Active Directory changes (Professional). You can get the Professional edition on a 30-day free trial.
3. Site24x7 – FREE TRIAL
Site24x7 uses its Network Configuration Manager (NCM) to control, back up, and restore device settings across routers, switches, firewalls, and other network hardware. By automating those tasks, the platform reduces manual effort and lowers the chance of configuration mistakes.
Version control makes configuration history easier to manage. Teams can track changes over time, compare revisions, and roll back to earlier states when needed, which helps preserve a dependable record of device settings.
Real-time change detection adds security and compliance value. When the platform spots a configuration change, it can notify administrators immediately so the modification can be reviewed against internal requirements and external policy obligations.
Scheduled backups improve recovery readiness by ensuring recent configurations are available if a device fails or needs replacement. Policy-driven controls, templates, and bulk changes further help teams standardize settings across larger environments.
Site24x7 delivers this capability as part of a wider hosted platform rather than as a stand-alone utility. You can try the service through a 30-day free trial.
4. Intruder
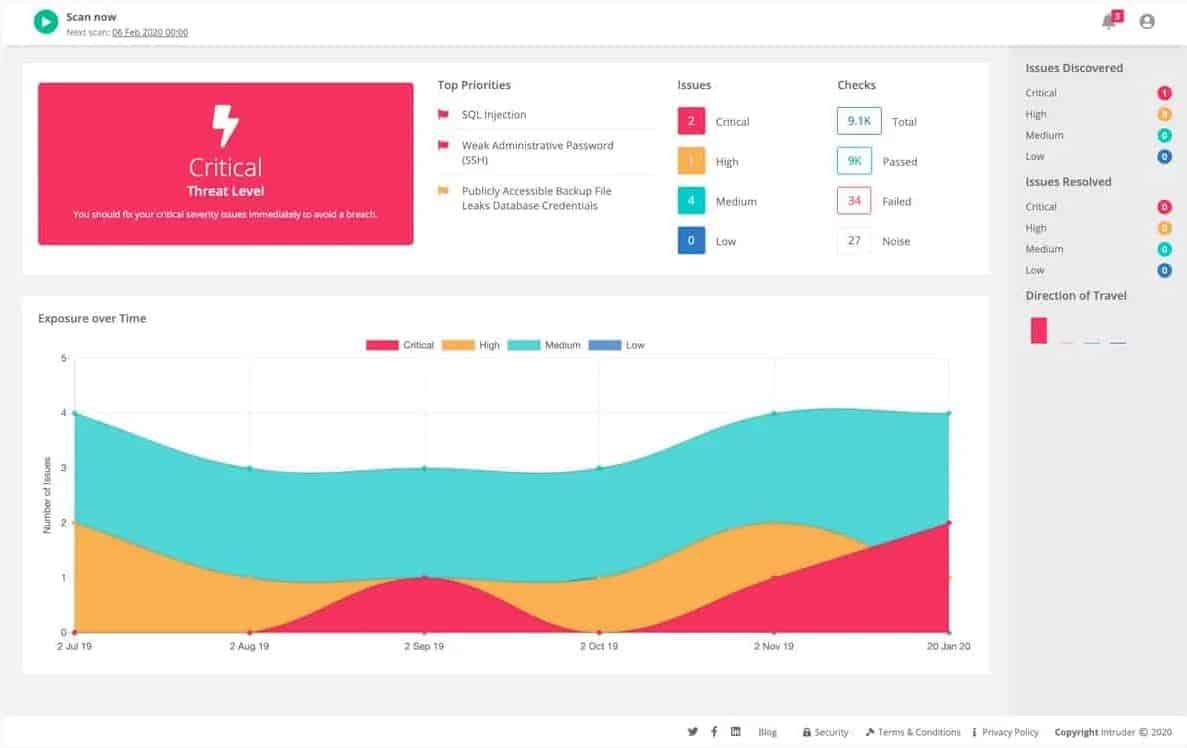
Intruder is a cloud-based vulnerability scanning tool. It’ll perform a detailed, monthly scan for every customer’s system, and will make an intermediate scan when a new threat appears in your service’s threat intelligence database.
Why do we recommend it?
Intruder’s cloud-based vulnerability scanning was a lifesaver in our security assessment. Its detailed monthly scans and immediate response to new threats ensured we stayed one step ahead of potential vulnerabilities. Intruder’s comprehensive scans covered every aspect of our IT infrastructure, leaving no stone unturned.
When you sign up for this service and create your account, Intruder will launch a full scan of your whole system looking for vulnerabilities. It will then do this monthly, as well as in the event of an intruder getting an update to the threat intelligence database. In these cases, it’ll automatically scan customer systems, looking at the hardware and software vulnerable to the threat in great detail.
Due to being a cloud-based service, Intruder looks at your network from the same perspective as most malicious agents. Its scans look through every part of the IT infrastructure present on the customer site, as well as any cloud services being used by the client. Intruder looks for over 9000 vulnerabilities, ranging from basic ones like SQL injections to more specific ones.
If you choose to install an agent on your network, this tool can also look at whether your network is weak to insider threats.
Who is it recommended for?
Intruder is recommended for businesses in need of cloud-based vulnerability scanning, suitable for various industries. For instance, a financial institution seeking robust cybersecurity measures and a small e-commerce business looking to fortify its online presence can both benefit from Intruder’s cloud-based vulnerability scanning. Its user-friendly approach works for both beginners and advanced users.
Pricing:
Intruder has three different subscription models. They are:
- Essential: You get one monthly scan
- Pro: You get a monthly scan, as well as a facility to allow on-demand scanning
- Verified: This plan gives you everything the previous two do, plus the aid of a human team of penetration testers.
Furthermore, this tool offers a month-long free trial.
5. SolarWinds Network Configuration Manager
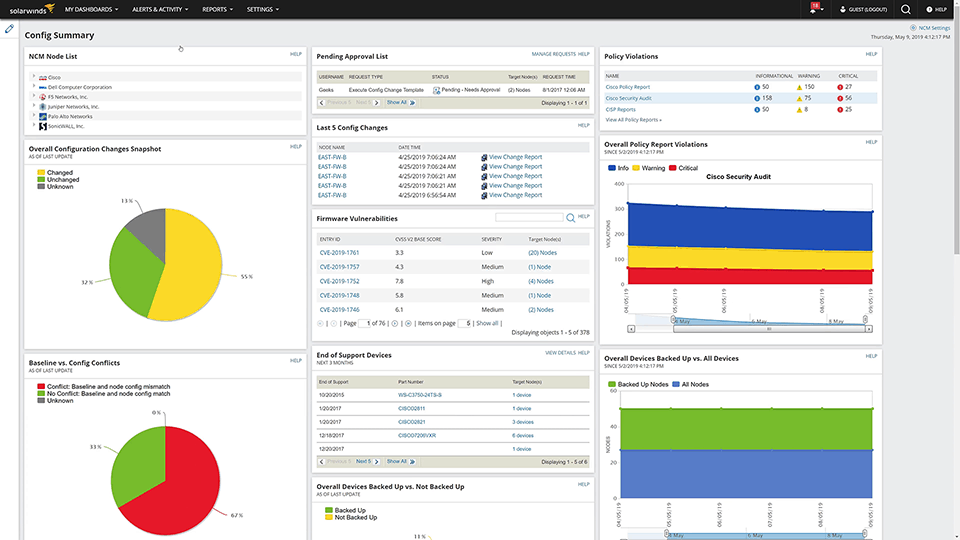
The SolarWinds Network Configuration Manager is an excellent tool for managing the configurations of your network devices. This device configuration & auditing tool allows you to deploy configurations to any device within your network, as well as take notice of unauthorized or incorrect configurations meddling with it.
Why do we recommend it?
In our rigorous testing, SolarWinds Network Configuration Manager stood out as a comprehensive solution. Its robust configuration management capabilities allowed us to deploy configurations seamlessly, and it promptly identified unauthorized changes, safeguarding our network’s integrity. The network vulnerability scanner was a lifesaver, constantly monitoring and auto-updating outdated devices.
Its network vulnerability scanner constantly tracks the whole network, and auto-updates any outdated devices. Its intuitive dashboard lets you take a look at a variety of different metrics and data to gain a good understanding of your network. It provides intuitive lists and graphs for metrics ranging from Overall Configuration Changes to Firmware Vulnerabilities.
There’s an abundance of other features such as alerts and reports. Its reporting ability allows you to create an audit report for the whole network or a specific device. The alerts feature notifies you whenever a configuration change takes place and gives you details on the changes made as well as the login ID that made them. If there’s an undesirable change, you’ll be able to roll back it as if it never happened.
Who is it recommended for?
SolarWinds Network Configuration Manager is recommended for businesses across various sectors that require top-notch network configuration management. It caters to both beginners and advanced users with its user-friendly interface. Different industries can have unique network configurations, and SolarWinds Network Configuration Manager provides the flexibility needed for customization. Whether you’re a small startup or a large enterprise, this tool is a valuable addition to your network management toolkit.
Pricing: SolarWinds comes with a free 30-day trial, after which it will cost you upwards of $3,085 USD.
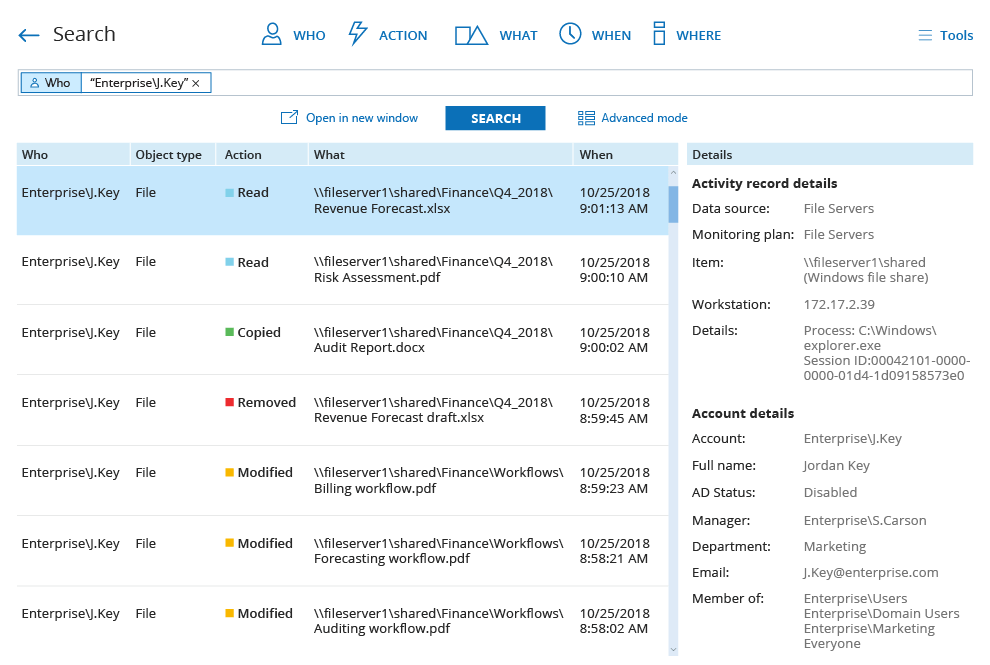
6. Netwrix Auditor
If you’re looking for a good tool to help you pay attention to configuration changes within your network, the Netwrix Auditor might just be the tool for you. You can see info on all system changes through its dashboard, such as Action, When, Where, Who, and What. This abundance of information is enough for you to understand the nature of the changes that happened.
Why do we recommend it?
Netwrix Auditor proved to be a valuable tool for monitoring configuration changes within our network. Its informative dashboard provided detailed insights into system changes, login attempts, and hardware monitoring.
The alert system was instrumental in notifying us of unusual events, and the ability to customize alert scripts streamlined our response to specific incidents.
Users can also see the info pertaining to login attempts, as well as any port scanning attempts. Failed logins are flagged with a red box, letting you spot attempts at breaking into your network at a moment’s notice. Furthermore, you can see all of the hardware monitoring info such as CPU temperature, or the status of your power supply or cooling fan.
The Netwrix also features an alerts system giving you automatic notifications for unusual events. You can also customize the scripts that the tool uses when an alert is made. You can use this to set up automatic Helpdesk tickets in case of specific events.
Who is it recommended for?
Netwrix Auditor is recommended for businesses looking to monitor and manage configuration changes effectively. Its user-friendly interface caters to both beginners and advanced users.
Its adaptable design allows small startups to efficiently monitor and manage configuration changes without overwhelming complexity. Medium-sized companies benefit from its scalable solutions, accommodating growing needs. For large enterprises, Netwrix Auditor’s comprehensive capabilities ensure effective configuration change oversight across complex networks, contributing to enhanced security and compliance.
Although its community edition is free, for a more in-depth look you’ll need to buy it. The price is determined based on a quote asked from the company directly, however, there is a 20-day free trial.
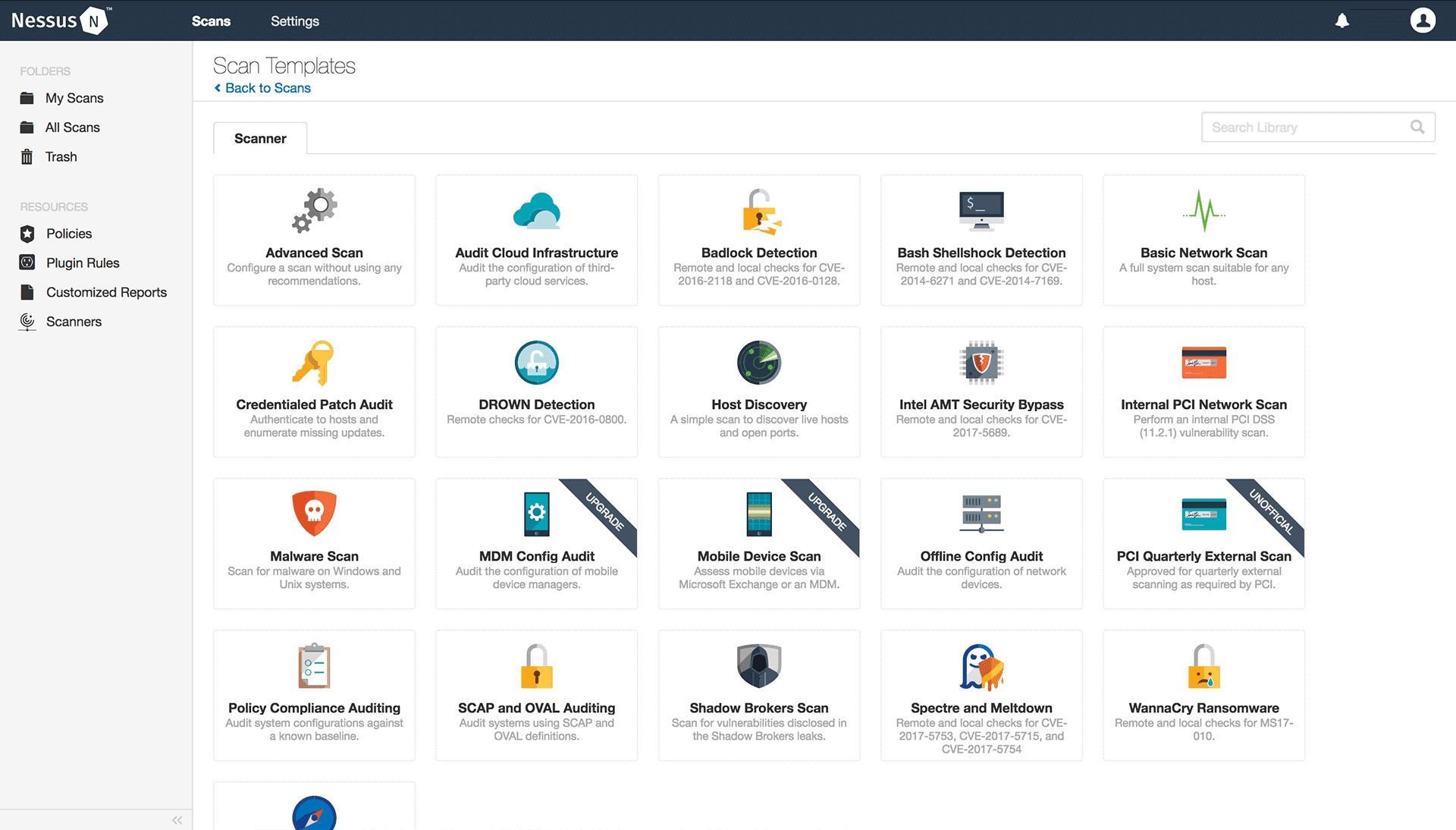
7. Nessus
Nessus is an excellent tool if you’re looking for a tool to handle config and patch management as well as auditing for free. This tool is updated with new plugins made to respond to new threats around averaging once a day. These plugins are automatically installed so you’re always ready to intercept malicious activity.
Nessus configuration is quite simple, mostly due to its 450 default configuration templates. The versatility of these templates, such as Basic and Advanced network scans, Malware scans, and WannaCry Ransomware scans makes it very simple to find the weaknesses you’re looking for.
Nessus also supports custom report generation to help reflect new entry points. It lets you make reports going into detail on vulnerabilities within a host or plugin. An example of this is the tool letting you make a Hosts Executive Summary report that lets you see a host breakdown showing them as one of the following:
- Info
- Low
- Medium
- High
- Critical
These reports can also be shared with your team in CSV, .nessus XML, and HTML format.
If you’re looking for a tool that’s well-equipped for dealing with brand new online threats, its free (Essentials) edition supports up to 16 IPs. There is also a paid Nessus Professional edition costing $2,390 USD which comes with a free trial.
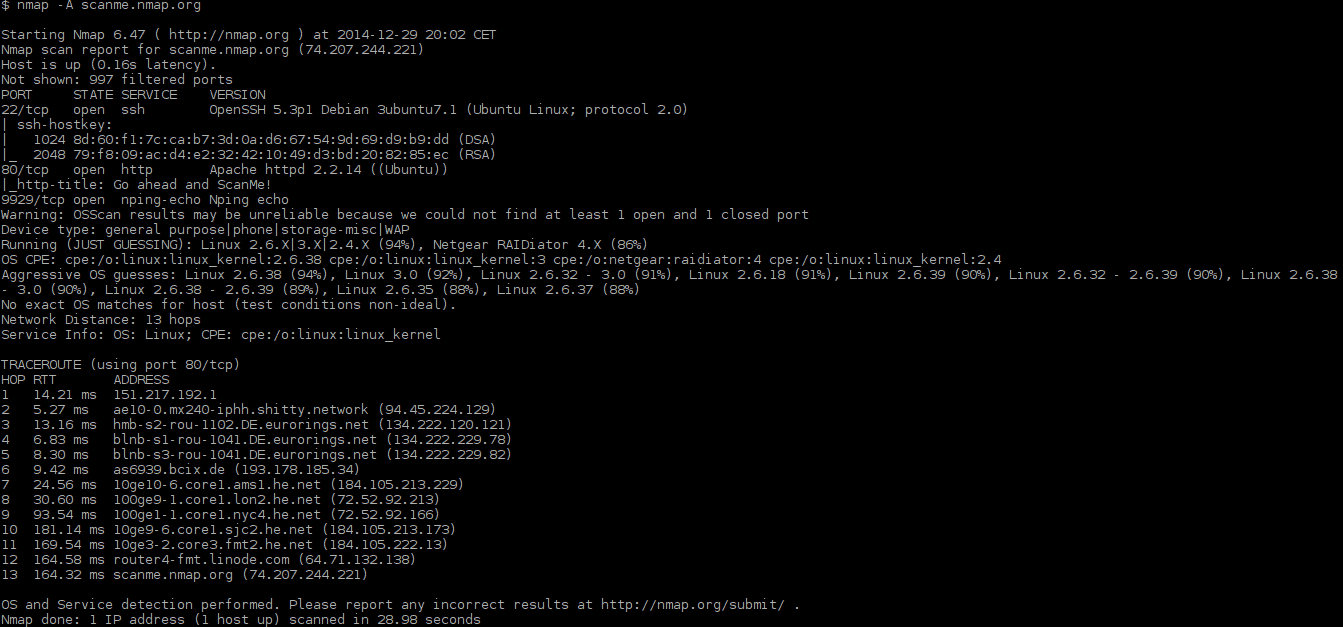
8. Nmap
Nmap is the first open-source tool on this list. It allows you to find hosts as well as vulnerable open ports. It’ll let you know the status of a chosen port through its command-line interface. You can also find more information on the entities found like their port, state, version, and service. Furthermore, you can find the OS version running software that can help you patch up obvious vulnerabilities.
Why do we recommend it?
An excellent choice for identifying hosts and open ports. Its simplicity makes it beginner-friendly, but its large feature set also appeals to advanced users. We relied on Nmap to detect vulnerabilities and patch them, contributing to our network’s security. Nmap efficiently addressed the challenge of network mapping and vulnerability identification.
Being open-source, Nmap, offers almost endless customizability, like its ability to do automatic scans by writing Lua scripts. Doing this can be a great asset as it can save the time it would take to run the scans manually. There is also the option to create automated scans. Nmap allows you to write scripts in Lua to run scans automatically. Automating scans is beneficial because it saves you time so that you don’t have to run scans manually to discover vulnerabilities.
If you’d prefer to interact with the tool outside of a command-line interface, Nmap has a GUI version called Zenmap. It lets you save scan profiles, as well as run the most common scans without setting them up manually, they can also be saved for later analysis.
It runs on Windows, Linux, UNIX, and FreeBSD.
Who is it recommended for?
Nmap is recommended for businesses seeking a versatile and cost-effective network mapping tool, suitable for various sectors. Its user-friendly interface caters to both beginners and advanced users. For large enterprises, Nmap’s advanced capabilities contribute to comprehensive security assessments, ensuring a robust defense against potential threats across complex network structures.
9. OpenVAS
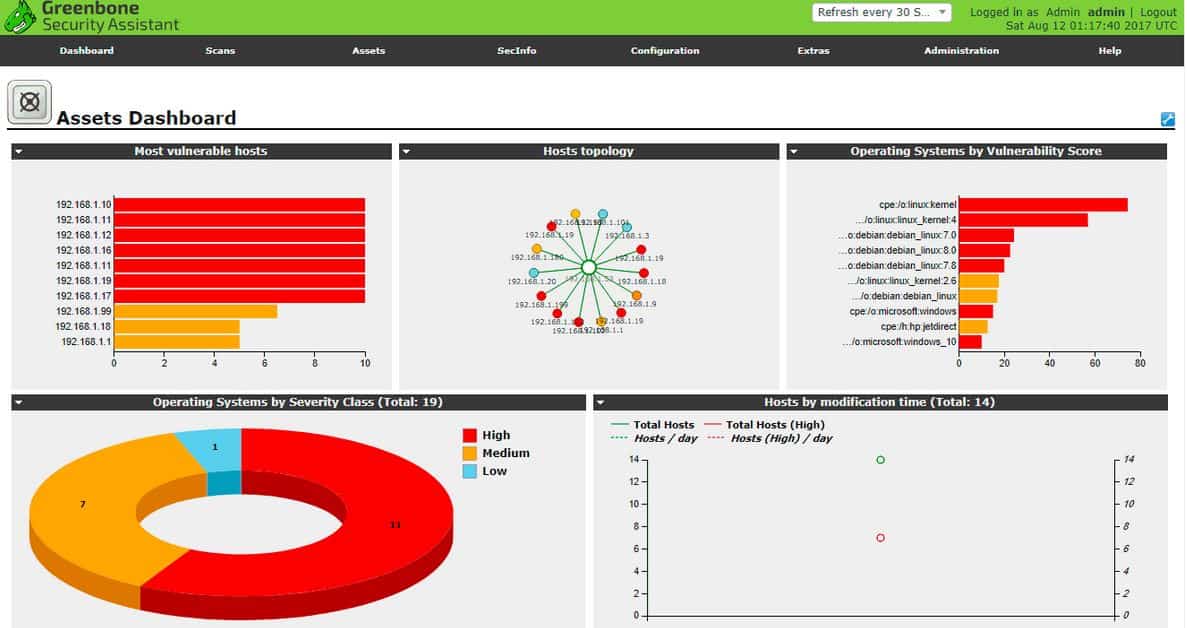
Last but not least, we have OpenVAS, an open-source vulnerability scanner targeted towards Linux users, letting you do both authenticated and unauthenticated testing. The tool receives constant updates through the Greenbone Network Vulnerability Tests feed, giving it access to over 50,000 weaknesses.
Why do we recommend it?
OpenVAS, as an open-source vulnerability scanner, was a reliable asset for authenticated and unauthenticated testing. Its constant updates ensured we stayed informed about over 50,000 vulnerabilities, contributing to a robust defense. OpenVAS addressed the challenge of vulnerability assessment effectively, making it a cost-effective choice for businesses.
Who is it recommended for?
OpenVAS is recommended for Linux users and businesses in need of an affordable yet effective vulnerability assessment. Its open-source nature aligns with the budgetary constraints of small startups, providing them with a cost-effective solution for vulnerability assessment. Medium-sized companies benefit from its adaptability, offering effective scanning tailored to their evolving needs. For large enterprises, OpenVAS scales efficiently, delivering comprehensive vulnerability assessments across expansive networks without compromising financial considerations.